Key Takeaways:
Blockchain security firm Slowmist flagged the attack via its Misteye threat intelligence system, identifying three rogue releases, namely versions 9.1.6, 9.2.3, and 12.0.1. The node-ipc package, used to enable inter-process communication (IPC) in Node.js environments, is embedded across decentralized application ( dApp) build pipelines, CI/CD systems, and developer tooling throughout the crypto ecosystem.
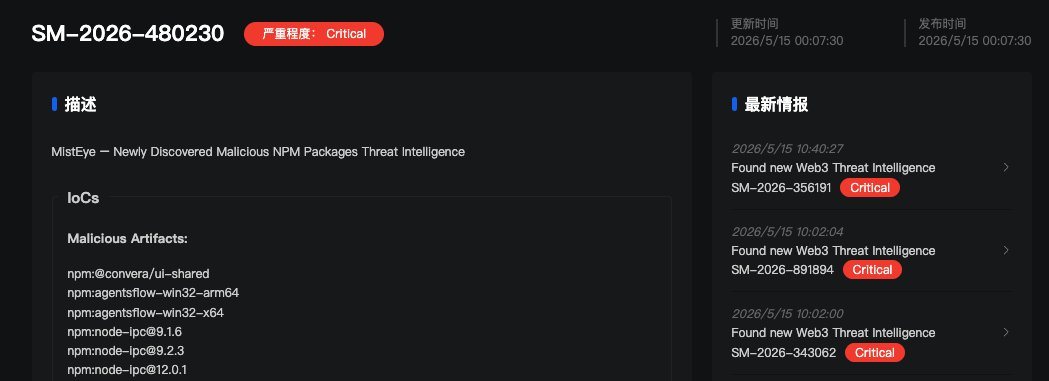
The malicious releases were identified as versions 9.1.6, 9.2.3, and 12.0.1.
The package averages over 822,000 weekly downloads, making the attack surface substantial. Each of the three malicious versions carries an identical 80 KB obfuscated payload appended to the package’s CommonJS bundle. The code fires unconditionally on every require(‘node-ipc’) call, meaning any project that installed or updated to the tainted releases ran the stealer automatically, with no user interaction needed.
The embedded payload targets over 90 categories of developer and cloud credentials, including Amazon Web Services (AWS) tokens, Google Cloud and Microsoft Azure secrets, SSH keys, Kubernetes configurations, Github CLI tokens, and shell history files. Pertinent to the crypto space, the malware targets .env files, which frequently store private keys, RPC node credentials, and exchange API secrets. Stolen data is exfiltrated via DNS tunneling, routing files through Domain Name System queries to evade standard network monitoring tools.
Researchers at Stepsecurity confirmed the attacker never touched node-ipc’s original codebase. Instead, they exploited a dormant maintainer account by re-registering its expired email domain.
The domain atlantis-software.net expired on January 10, 2025, with the attacker re-registering it via Namecheap on May 7, 2026. They then triggered a standard npm password reset, gaining full publish access without the original maintainer’s knowledge.
The malicious versions remained live on the registry for approximately two hours before detection and removal. Any project that ran npm install or auto-updated dependencies during that window should be treated as potentially compromised. Security teams have recommended auditing lock files immediately for versions 9.1.6, 9.2.3, or 12.0.1 of node-ipc and rolling back to the last verified clean release.
Supply chain attacks on the npm ecosystem have become a persistent threat in 2026, with crypto projects serving as high-value targets due to the direct financial access their credentials can provide.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



