1. Introduction - The "Singularity" of Odyssey
The Web3 incentive mechanism is currently at a singular point of returning from the "illusion of traffic" to the "essence of value." Over the past few years, the Odyssey model has gone through a baptism from peak to bottleneck, and we find that simple model replication can no longer stir ripples in the world of information overload on the chain.
1.1 Paradigm Shift: Why are Most Projects' Odyssey Outcomes Minimal?
Although the Odyssey model has created many myths of wealth creation, as we enter 2026, developers find that simply mimicking leading examples has become difficult to generate an "outreach effect." This unsatisfactory situation is fundamentally due to a deep fracture between the logic of incentives and the user ecosystem.
- Increased Incentive Entropy Has Led to Serious Homogenization and Involution
When 90% of the projects in the market are asking users to repeatedly "cross-chain, stake, forward" to obtain almost identical "points," the marginal return on user attention begins to drop sharply. This model replication has led to increased incentive entropy— the scarcity of rewards is diluted by a plethora of homogenized projects. For example, with Linea "The Surge" and the subsequent emergence of various L2 point battles, when users find themselves needing to transport liquidity across dozens of logically similar protocols only to receive continuously shrinking inflation points, aesthetic fatigue evolves into a state of "lying flat," and the incentive effect is completely consumed in endless involution.
- The Lack of Game Mechanisms in "Witch-style Growth" Creates Vast Amounts of False Prosperity
Many project teams have only learned the superficial appearance of the "task wall" while neglecting the deeper anti-witching game, resulting in most incentives being siphoned off by automated scripts (Farmers) from professional studios. The experience of zkSync Era serves as a typical warning: although it boasts over 6 million active addresses on the surface, in-depth data reveals that the vast majority are mechanical interactions created solely for taking advantage of opportunities. This "paper prosperity" not only triggered a huge community governance crisis during the TGE phase but, more importantly, 90% of addresses swiftly reverted to zero after the airdrop, leaving the project team with high customer acquisition costs without any real ecological foundation.
- The "Disconnection" Between Product Logic and Incentive Interaction Makes Participation Mechanical
The outreach effect often stems from the deep coupling of a product's core functionality and its reward mechanism. If the Odyssey tasks turn into "on-chain labor" unrelated to product value (for example, requiring privacy protocol users to publicly post on Twitter), users cannot develop brand identification. Similar to early DeFi projects that forcibly bundled social tasks on platforms like Galxe, they gained tens of thousands of followers in a short time but attracted mostly low-net-worth task seekers due to this "mismatch of demand," leading to the loss of substantial fund users who were turned off by this Web2-style forced interaction. Once the tasks end, total locked value (TVL) often sees a sharp decline within 24 hours, failing to form any emotional resonance or competitive barrier.
1.2 Defining Win-Win: Protocol Unit Economic Benefit (Unit Economy)
To break the deadlock of "ineffective outcomes," the logic of win-win must shift from "buying traffic" to "building ecology." We need to seek balance at the mathematical level:
1.2.1 Unit Marginal Benefit on the Protocol Side
Project teams need to recognize that the essence of Odyssey is the precise customer acquisition cost (CAC).
UnitMargin=LTVuser−CACincentive
Only when the long-term fees, liquidity stickiness, or governance contributions (i.e., LTV) generated by users in the protocol exceed the rewards (Incentive), does Odyssey transform from mere "money dispensing" to sustainable capital expansion.
1.2.2 Total Utility Capture on the User Side
Users’ pursuits in future Odysseys will become more rational. They are no longer content with "points that may go to zero" but calculate the overall return rate:
- Airdrop: Immediately convertible token shares.
- Utility: Long-term rights in the protocol (such as lifetime reduction in fees, RWA profit shares).
- Reputation: On-chain credit assets. This is the core credential for gaining access to the future top project's "entry whitelist."
1.3 Core Assumption: Incentives are Not Just Tokens, but a Composite of Credit, Privileges, and Rights to Earnings
In-depth incentive design completely overturns the old assumption that "ERC-20 tokens are the only driving force." An Odyssey capable of producing an outreach effect must have the following three-dimensional value support:
- Credit (Credit/Identity)
Through soul-bound tokens (SBT) or on-chain identity systems, users’ contributions are permanently solidified. Credit is not only a badge but also an efficiency multiplier: high-credit users can unlock "no-deposit lending" or "task weight bonuses," giving real contributors an advantage beyond scripts.
- Privileges (Privileges/Utility)
Embedding rewards into usage rights of the product. For example, winners of the Odyssey can receive a "veto right medal" in protocol governance or "primary mining rights" for other new projects within the ecology. Privileges turn users from "passers-by" into "long-term holders" of the protocol.
- Revenue Rights (Revenue Rights/RWA)
As compliance advances, the most appealing Odyssey in 2026 begins to introduce underlying dividend logic. Rewards are no longer just inflationary air but are anchored to the protocol's actual revenues (such as RWA bond interest, Dex transaction fee sharing). This injection of real yield is a trump card for projects to stand out in a bubble and achieve genuine outreach.
2. User Behavior Spectrum: From "Wool Puller" to "On-chain Citizen"
In the future on-chain ecology, the traditional definition of "user" has collapsed. With the popularization of Chain Abstraction and AI agents, the soul (or algorithm) behind the addresses shows a high degree of differentiation. Understanding this spectrum is a prerequisite for designing a win-win incentive mechanism.
2.1 User Layering Model: Deep Portrait Based on Motivation and Contribution
We divide participants in the Odyssey into three representative Greek letter layers, this layering is no longer based solely on asset scale (TVL) but based on behavioral entropy and protocol loyalty.
2.1.1 Player Layering
Gamma - Arbitrageurs (AI Bounty Hunters)
- Role Definition: AI bounty hunters pursuing extreme efficiency.
- Psychological Motivation: Highly rational. They have no interest in the project itself; the only coordinates are "risk-free interest rate" and "certain returns."
- Behavioral Performance: Typical script-driven interaction, with very low latency. They swarm in gas fee valleys like migratory birds, their behavioral paths are highly standardized and homogenized.
Beta - Explorers (Hardcore Players)
- Role Definition: Hardcore players deeply participating in the ecology.
- Psychological Motivation: Resonance-driven. They value in-depth experiences of the product, community identity, and future long-term rights.
- Behavioral Performance: Actively participate in in-depth function testing, proud of obtaining rare badges (SBT). They provide high-quality feedback in the community, and their interaction traces display significant personal color and subjective preference.
Alpha - Builders (Pillars of the Ecology)
- Role Definition: The fundamental support and interest community of the protocol.
- Psychological Motivation: Sovereignty-driven. Their goals are long-term governance rights, dividend rights of the protocol, and creating an unbreakable security moat.
- Behavioral Performance: Demonstrated by locking large amounts of capital for long periods, submitting core code proposals, or running validation nodes. As mentioned in the text: "They do not produce noise, only create credit."
2.1.2 Behavioral Characteristics and Quantitative Models
- Gamma's Survival Rule: Ruthless cost estimation
For Gamma players, an Odyssey is a finely calculated game. They do not care about the project vision; only capital efficiency within a unit of time matters to them.
- Alpha's Moat Effect: The Game of Power
Alpha players disdain retweeting likes on Twitter; their Odyssey is reflected in sovereign contributions. They are the "stabilizing force" of the protocol, and their large asset reserves and maintenance of technical nodes directly determine the protocol's market cap limit and risk resistance.
2.1.3 Identity Collapse and "Consensus Alchemy"
Identity is not lifelong; it is a dynamically evolving continuum. In excellent Odyssey design, user identity undergoes "quantum leaps":
- The Leap from "Arbitrage" to "Exploration": A Gamma player initially only motivated to take advantage may become moved by the protocol's ultimate product experience or robust technical logic during in-depth interaction. When they find that the long-term benefits of holding exceed the immediate profits of selling, they undergo "identity collapse"—transforming from "taking advantage and leaving" to "deep holding."
- The Project's "Consensus Capturing Power": This leap is essentially an "alchemy" that the project team performs on users. Low-quality projects can only attract and retain arbitrageurs, ultimately collapsing with the depletion of incentives; while quality projects have a centripetal force that can transform "bounty hunters" into "guardians."
Core Insight: The incentive mechanism is no longer a rigid divide-and-conquer tactic but rather a process of screening, filtering, and transforming. It acknowledges the existence value of Gamma, but its ultimate mission is to leverage incentives to guide users through a tiered evolution from profit-seeking individuals to value partners.
2.2 Behavioral Heatmap Analysis: Non-linear Characteristics of Mainstream Layer 2 Task Completion Paths
Before 2024, the Odyssey task paths were linear (Step One: Follow on Twitter; Step Two: Cross-chain; Step Three: Swap). However, in the future, the "intent-centric" design will make the users' behavioral heatmap show significant non-linearity and mesh characteristics.
2.2.1 Path Forking from "Task-driven" to "Intent-driven"
Through the latest data mining of mainstream L2, such as Arbitrum, Optimism, and Base, we have discovered:
- Path Uncertainty: For the same Odyssey task, User A might complete it by "lending -> staking -> minting," while User B might achieve it through "full-chain aggregator -> automated strategy pool" with one click.
- Cross-chain Heat Anchor Points: Behavior is no longer limited to a single chain. User behavior in Layer 2 is often accompanied by immediate feedback on Layer 3 dedicated application chains. For instance, after 10 minutes of L2 interaction, the heatmap shows users quickly triggering automatic reward distribution scripts on the related AI chain.
2.2.2 Non-uniform Distribution of Behavioral Entropy
Monitoring data indicates that high-quality users (beta and alpha layers) present behavioral heatmaps with higher "complex entropy."
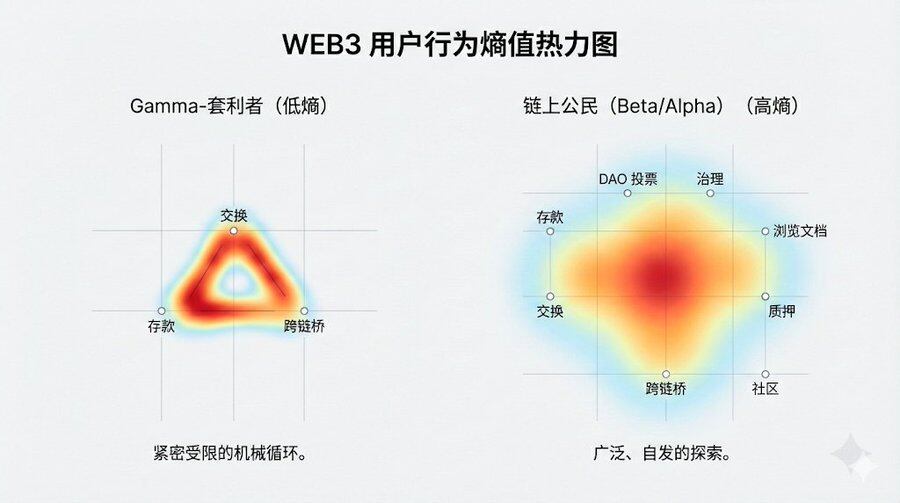
- Gamma's Heatmap: Displays a high degree of mechanical regularity. Interaction points are concentrated within the minimal closure required by tasks, with short and repetitive paths.
- On-chain Citizens' Heatmap: Shows diffusion and long-tail characteristics. Besides completing established Odyssey tasks, they also explore secondary pages of the protocol, read on-chain documentation, or interact with other dApps within the ecology.
Insight: The most successful Odyssey projects have heatmaps that are not a straight line but a gravitational field. It can attract users to voluntarily linger within the ecology and generate “unplanned” interactions after completing the designated tasks.
Users no longer wish to be regarded merely as a "wallet address." In Odyssey 3.0, the end of the behavioral spectrum culminates in "on-chain citizenship." This citizenship signifies not only reward distribution but also an endorsement of identity in a multi-chain civilization.
3. Mechanism Design: Ensuring Win-Win Through Mathematical Models and Game Balance
Throughout the evolution history of Web3, early Odysseys have often been criticized for falling into "Ponzi deadlock": project teams swapping future inflation expectations for current false prosperity. To escape this vicious cycle, the focus lies in achieving incentive compatibility. This means we need to ensure that users' paths of pursuing maximum personal interest completely align with the protocol’s long-term healthy development through rigorous mathematical models.
3.1 Incentive Compatibility Equation (The IC Constraint): Reconstructing Costs and Benefits Game
In traditional airdrop models, the marginal cost of Sybil attacks is nearly zero. To protect the interests of honest contributors from being diluted, future Odyssey designs will introduce game-theoretic IC constraint equations.
Core Game Model
Let R(c) represent the total comprehensive reward obtained by honest users during real interactions, and C(c) the hard costs incurred (including gas fees, slippage, funds utilization time, etc.). Meanwhile, let E[R(s)] be the expected gain from automated script interactions by Sybil attackers, and C(s) represent their attack costs (including server, IP pool, anti-detection algorithms, and sunk costs after being cleaned).
To achieve a win-win Nash equilibrium, the following must be satisfied:
Interventions and Evolutions in the 2.0 Era:
- Significantly Increase C(s) (Attack Resistance): In future years, defenses will no longer rely on simple blacklists but rather introduce AI behavioral entropy detection. The system will analyze the spatiotemporal distribution of interactions, the associated entropy of funding links, and the "human-like nature" of operations. For suspicious accounts, the system will dynamically implement a "gas fee punitive coefficient," requiring them to pay higher transaction fees during non-mainstream periods, thereby directly destroying the unit profitability of scripts.
- Deeply Optimize R(c) (Benefit Structure): The reward pool shifts from "pure governance tokens" to "hybrid equity packages." This includes: cash flow rights: direct distribution of protocol transaction fee dividends (Real Yield). Privilege assets: permanent fee reductions (Gas Rebates) or interest bonuses for cross-protocol lending. Governance leverage: granting governance weight bonuses to long-term holders, ensuring that "real participation" not only generates wealth but also power.
3.2 Dynamic Difficulty Adjustment Mechanism (Dynamic Difficulty Adjustment, DDA)
The future Odyssey will no longer be a static task list. Drawing on Bitcoin's difficulty adjustment algorithm, advanced protocols will begin implementing dynamic difficulty adjustment (DDA).
Operational Logic:
When the Odyssey enters a burst period, with the total number of interaction addresses and total locked value (TVL) surging in a short time, the system will automatically sense "overheating." At this point, the points capture algorithm will automatically trigger an increase in difficulty:
- Increasing Funding Thresholds: The amount of interaction or liquidity lock-in period required to obtain the same points will increase.
- Upgraded Task Complexity: Transitions from simple "one-click Swaps" to "multi-protocol combination strategies" (e.g., lending on Protocol A, staking on Protocol B, hedging on Protocol C).
Win-Win Logic:
- For the protocol: DDA acts as a safety valve, preventing the influx of speculative traffic from overwhelming liquidity pools, avoiding cliff-style crashes due to "reward exhaustion."
- For alpha-citizens: It protects those early, stable builders. High-difficulty tasks naturally filter out "wool pullers" lacking specialized capabilities, allowing reward shares to be more accurately directed to high-net-worth genuine users.
3.3 Value Proof Model (Proof of Value, PoV)
In Odyssey 3.0, "the number of addresses" has been thoroughly deemed a vanity metric. Project teams are now fully transitioning to the PoV model, which focuses on measuring contribution density.
Contribution Density Formula:
We define contribution density D as:
D=∑(Liquidity×Time)+γ×Governance_ActivityTotal_Reward
- Liquidity (Capital Stickiness): Measures how long user funds remain "deposited" within the ecology, rather than withdrawn immediately.
- gamma (Community Contribution Factor): This is a regulating variable. For users actively participating in governance votes, writing technical documents, or generating real positive ripples in social networks, gamma participation can reach 2x or even higher.
- Total Rewards: As the denominator, aimed at balancing inflation, ensuring the value of unit rewards.
Deep Analysis of Win-Win:
Through the PoV model, project teams gain not just a list of cold wallet addresses but a genuine map of ecological participants. Users find that because of the gamma factor, their "labor," rather than mere "capital," can achieve extremely high returns. This mechanism achieves a harmonious resonance between capital efficiency and human creativity, ensuring that Odyssey is no longer merely a "digital game," but a real process of value co-creation.
4. Technical Pillars: Behaviorally Perceptive ZK Incentive Underlying Protocol
In the future paradigm shift, Odyssey will no longer be a front-end "task wall," but an underlying protocol capable of automatically capturing, analyzing, and transforming user behavior. This protocol builds a closed loop from behavioral perception to precise incentives through ZK technology and full-chain abstraction.
4.1 Behavioral Perception Engine: From "Passive Check-ins" to "Full-chain Behavior Tracking"
The core functionality of this protocol is to act as a full-chain data crawler and indexer. It no longer relies on users to manually submit task screenshots but automatically records users’ deep interactions within DApps through underpinning gateways.
- Omni-dimensional Behavioral Modeling: The protocol can real-time capture users' liquidity depth, transaction frequency, governance participation, and even dwell time on product frontends (through zero-knowledge off-chain proofs).
- Dynamic Weight Analysis: The protocol will multidimensionally model these behaviors, analyzing whether the user is a "long-term holder (HODL)," "high-frequency liquidity provider," or a "deep governance participant." This analysis, based on real interactions, evolves the Odyssey model from “mechanical tasks” to “behavioral badges.”
4.2 ZK-Proof Driven Privacy Analysis and Filtering
Once behavioral data is acquired, the protocol utilizes ZK-Proof (zero-knowledge proof) technology to achieve precise filtering without disclosing users' wallet details and privacy data (PII).
- ZK-Credentials Credit Endorsement: Users do not need to "show their face" or expose asset details. Through this underlying protocol, users can present “high-net-worth user proof” or “senior DeFi player proof” generated by the protocol to project teams.
- Filtering Effect and Anti-Witching: The protocol allows project teams to set "high-level entry thresholds." For instance, using ZK-STARKs to verify a user’s non-repetitive interaction over the past 180 days, generating a "unique real human proof." This locks in the space of automated scripts (Farmers) at the foundational level, ensuring incentives flow only to those recognized by the protocol as having "high-quality behavior."
4.3 Intent-driven Full-chain Abstraction Incentives (Intent-centric & Abstraction)
This protocol not only records behaviors but also simplifies participation paths through an intent engine (Intent Engine), allowing interaction to equal incentives.
- Intent-driven Automatic Interaction: Users only need to express the intent of "I want to participate in the liquidity incentive of this protocol," and the underlying protocol will automatically coordinate cross-chain asset transfers, gas fee balances, and contract calls.
- Immediate Transformation and Win-Win: This "interaction-free, automatic incentive" model spares users from the cumbersome on-chain steps; while project teams capture users' most genuine core intentions through the underlying protocol, not only improving conversion rates but allowing the Odyssey model to truly return to the product value itself.
5. Future Evolution - From "Marketing Activities" to "Normalization Incentive Protocols"
The future Odyssey will completely bid farewell to "time-limited" characteristics, evolving into a resident growth module (Native Incentive Layer) at the protocol code level.
5.1 Embedded Incentives (GaaS: Growth-as-a-Service)
Odyssey will no longer exist as a webpage, but rather a dynamic reward logic embedded within smart contracts.
- Evolution: As long as users generate positive value with the protocol (such as reducing slippage, providing long-term liquidity), the contract will automatically recognize and distribute rewards in real-time. The Odyssey has become the protocol’s "autopilot mode."
5.2 Cross-protocol "Credit Lego" (Interoperable Incentives)
Future Odyssey points will be portable. Your Odyssey performance in the A lending protocol will translate into initial levels in B social protocol through ZK proof.
- Ultimate Form: A universally applicable "on-chain contribution score" will replace fragmented points. This cross-protocol interaction will facilitate the ultimate leap of the Web3 ecology from “stock mutual cutting” to “incremental co-building,” achieving true global on-chain commonwealth.
6. Practical Execution Guide (The Executive Playbook)
Odyssey is no longer a "throw money and leave" game but an extremely sophisticated ecological diversion and capital solidification project. For project teams, the core of execution lies in balancing "the explosive power of traffic" and "the system's resilience." Here are 10 execution golden rules and practical frameworks to ensure a win-win situation.
6.1 Paradigm Shift in Core KPIs: From "Vanity" to "Hard Core"
Do not be deceived by the number of Twitter followers and addresses anymore. In a future where intent engines can cheaply simulate millions of addresses, these metrics are easy to fabricate.
- Metric A: Sticking TVL (Sticky Capital Percentage). The calculation formula is as follows:
RetentionRatio=TVLT+90TVLPeak
If this ratio is below 20%, it indicates a serious defect in incentive mechanism design.
- Metric B: Net Contribution Score (Net Contribution Score). This is the ratio of the total protocol transaction fees generated by a single address to the incentive costs they received.
- Metric C: Governance Active Entropy Value. Measures the actual depth of Odyssey user participation in Snapshots or on-chain proposals, rather than just vote stuffing.
6.2 Modular Task Design: Building a Ladder "Funnel"
The most successful Odysseys typically adopt a "three-tier" structure intended to convert massive traffic into core citizens.
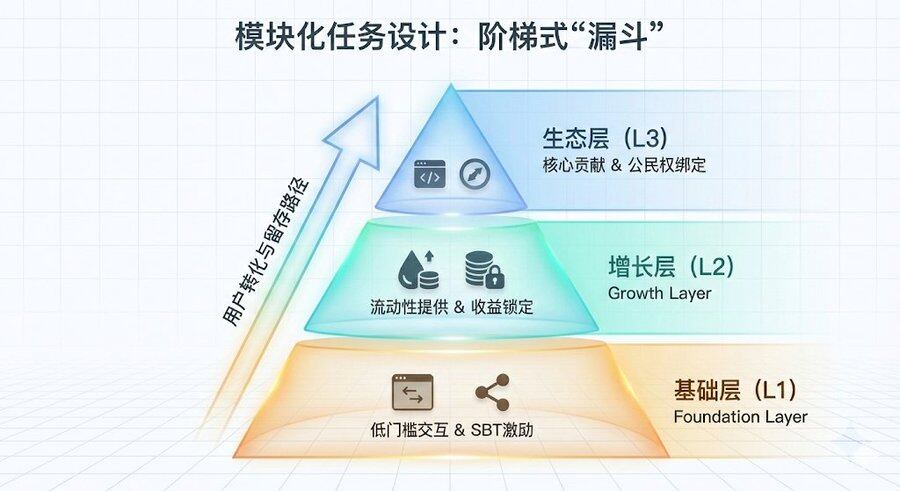
Basic Layer (L1) — Breaking the Ice and Reaching Out
- Target Audience: New users / General Web3 players
- Core Task: Complete basic interactions (such as one-click Swap, social sharing)
- Incentive Structure: Grant non-fungible badges (SBT), accumulate future airdrop points
- Retention Logic: Extremely low barriers. Establish the first touchpoint through SBT, allowing users to leave a "digital footprint" in the ecology.
Growth Layer (L2) — Liquidity Engine
- Target Audience: Active traders / liquidity providers (LP)
- Core Task: Provide deep liquidity, manage combined positions, cross-chain staking
- Incentive Structure: Protocol native token rewards, real-time transaction fee discount cards
- Retention Logic: Yield (APY) game. By locking funds at high efficiency, artificially increase the "opportunity cost" of withdrawing.
Ecological Layer (L3) — Core Sovereign Faction
- Target Audience: Core contributors / developers / governance representatives
- Core Task: Write technical documentation, submit code patches, initiate effective governance proposals
- Incentive Structure: Governance weighting factors, RWA revenue dividend rights, ecological whitelists
- Retention Logic: Grant "citizenship." Not just benefit distribution but long-term interest bundling, turning contributors into the masters of the ecology.
6.3 Risk Control and "Circuit Breaker" Design
During the Odyssey execution process, it is easy to encounter "wool puller raids" due to market volatility or mechanism loopholes.
- Dynamic Incentive Coefficient Adjustment: Establish a dynamic adjustment system based on on-chain congestion conditions. When daily interactions trigger thresholds (for example, exceeding a baseline of 500%), the system will automatically reduce the point coefficient for that period, preventing scripts from violently brushing volume during low-cost phases.
- Pre-emptive Anti-Witching: Refusing "post-cleaning." On the first day of the activity launch, utilize an AI behavioral fingerprint system to perform "shadow tagging" of suspicious addresses. These addresses can complete tasks normally but can only enter a "low-yield pool."
- Liquidity Mitigation Mechanism: All rewards should not be released in one go at TGE. Introduce a yield smoothing mechanism (for example, unlocking rewards over 6-12 months based on user activity post-Odyssey), enforcing “long-term incentive compatibility.”
6.4 "Preemptive" Experiment in Community Governance
Do not wait until after the issuance of tokens to begin DAO governance.
- Simulated Voting Tasks: During the Odyssey phase, set "simulated voting on an improvement suggestion for a particular protocol parameter" as a high-weight task.
- Purpose: This can筛选 out alpha citizens who truly care about the development of the protocol while also cultivating community governance habits in advance, lowering future communication costs during real governance.
6.5 Execution Check-list (Must Read Before Launch)
- Value Closed Loop Check: Does the source of rewards include the protocol's own revenue (Real Yield)?
- Anti-Witching Depth: Have ZK-ID or real person identification systems (such as World ID / Gitcoin Passport) been integrated?
- Capital Stickiness: Do tasks require funds to remain within the protocol for over 14 days?
- Technical Redundancy: Can the protocol contracts withstand 100 times the usual call volume in an instant?
- Emotional Value: Does the narrative of tasks have social disseminative properties rather than being merely "digital transportation"?
Conclusion - From "Game Confrontation" to "Value Symbiosis"
The Odyssey model, at its core, is a revolution about selection efficiency. When we introduce the “Incentive Compatibility Equation” and “Behavioral Entropy Analysis” in the text, the goal is not only to defend against witching attacks but also to establish a precise measure of value in a decentralized anonymous network.
Under this new paradigm, project teams and users are no longer zero-sum adversaries. Through dynamic difficulty adjustment (DDA) and the value proof (PoV) model, we successfully transform simple financial interactions into quantifiable contribution density. This transformation brings about a critically important by-product—on-chain credit.
Credit does not arise from thin air; it is the "digital residue" that accrues from countless high-entropy interactions, long-term lock-ins, and governance participation. In the future ecology, incentive mechanisms will no longer just be tools for distributing tokens but will become crucibles for forging credit. They ensure that every genuine contribution is remembered in code, making “credibility” a more scarce passport than capital itself.
Ultimately, the end of Odyssey is not the end of a single airdrop but the starting point of the protocol and citizen contract relationship. As we dissipate the bubble of traffic using mathematics and technology, the solid foundation of credit left behind is fundamentally the guarantee of Web3's transition from a "speculative wasteland" to a "value civilization."
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。


