This week in East Eight Zone time, Bonk.fun/Letsbonk.Fun was reported to have its domain hijacked by hackers, triggering high alert in the community. The attackers infiltrated team accounts and implanted a coin-stealing program; once users continue to access related domains, connect wallets, and authorize, their assets might be quietly transferred away. The project team immediately prioritized the warning "Do not visit bonk.fun related domains," paused traffic and interaction guidance, and made the safety of user assets their only priority. Behind this incident lies a more glaring contradiction: assets are decentralized and hosted on-chain, while access points rely on extremely centralized and fragile DNS and front-end hosting. This article will take the Bonk.fun incident as a starting point, extending to the misalignment and game between Web3 front-end security, compliance regulation, and capital entry, sorting out the deeper structure of this "entry battle."
Domain Hijacking: From Warning Announcement to Risk Spillover
● Overview of the Attack Path: According to public information, the attackers first gained control of the team account related to Bonk.fun, deploying or embedding malicious code on the front end, causing wallet interactions on the accessed page to be "switched," turning into a concealed coin-stealing program. Since the briefing did not disclose technical implementation details or confirm whether specific contract layers were affected, it can be determined that this was an account and domain layer security incident focused on the front end, rather than a traditional on-chain vulnerability exploitation.
● Urgent Announcement Rhythm: After the incident was exposed, the project team released a very direct statement to the community—"Do not visit bonk.fun related domains." They repeatedly emphasized that the team was "prioritizing user asset security for processing." This kind of wording reflects that risk assessments have pointed to the entry layer being completely unreliable, and on the other hand indicates that before the technical repair plan is finalized, pausing all traffic and interactions is the quickest means available for them to stop the bleeding.
● Real Risk Path Facing Users: For ordinary users, risks do not occur within complex contract calling logic but appear in seemingly "safe and familiar" browser address bars. When they enter the page via official links or search results, click "connect wallet," and then sign authorizations according to prompts, malicious scripts can easily steal tokens or NFTs within the permission scope. This type of front-end hijacking often circumvents the on-chain security defenses people associate with "code audits" and "multisig custody," directly exploiting people's trust inertia in domains and brands.
● Boundaries of Uncertainty: As of now, there are no authoritative channels disclosing specific amounts stolen, number of victims, or identity information of the attackers. Research briefings also clearly listed the precise point of time of the incident, progress in tracking the attackers' wallets, and other information as missing or to be verified. This means we can only discuss confirmed risks and responses, and cannot make any inferences regarding the scale of losses, internal responsibilities, or technical profiles, to avoid replacing facts with imagination.
Why Decentralized Assets Are Dragged Down by Centralized Entry
● Mismatched Reality of Assets and Access Points: Most current Web3 applications rely on public chains and wallets to achieve decentralization at the asset custody and transaction settlement level, yet at the access entry level, they still heavily depend on DNS domains, traditional servers, and centralized CDNs. This creates a mismatch: assets are "on-chain," while the entry point is "in the cloud." The former is tamper-proof, while the latter continues to adhere to the security model of Web2; once a domain or hosting account is breached, users are not directed to the "decentralized application" they think they are reaching.
● Demonstrative Effect of Bonk.fun: In the Bonk.fun incident, attackers did not need to crack private keys or bypass on-chain permission controls; rather, they directed users to pages containing malicious scripts by controlling the domain and front-end hosting layer. As long as the interaction interface looks "similar to before," most users find it hard to notice that the underlying code has been replaced, and on-chain security audits and contract multisigs can thus be bypassed, turning into a fort "guarding an empty city."
● Invisible Risks of Single Point Security: Users are accustomed to seeking a single entry from official Twitter, Discord announcements, and search engine results, considering it an "absolutely safe" trust anchor. When this single entry is hijacked, the entire user base becomes exposed to the same risk. For many new users, they do not possess the ability to verify front-end code or signature content, and can only place their trust on a short domain; this highly centralized and fragile trust structure is inherently contrary to the spirit of decentralization.
● Renewed Discussion on Decentralized Front Ends: After the Bonk.fun incident, discussions about decentralized front ends, multiple access points, and content addressing have once again heated up in the community. Some viewpoints advocate lowering the probability of single point breaches through multiple domain redundancy, front-end code open-source hosting, or even using on-chain or distributed storage systems. However, these remain largely in the exploratory stage and trend discussions, and still face practical obstacles in technology, experience, and compliance in becoming an industry consensus and large-scale implementation.
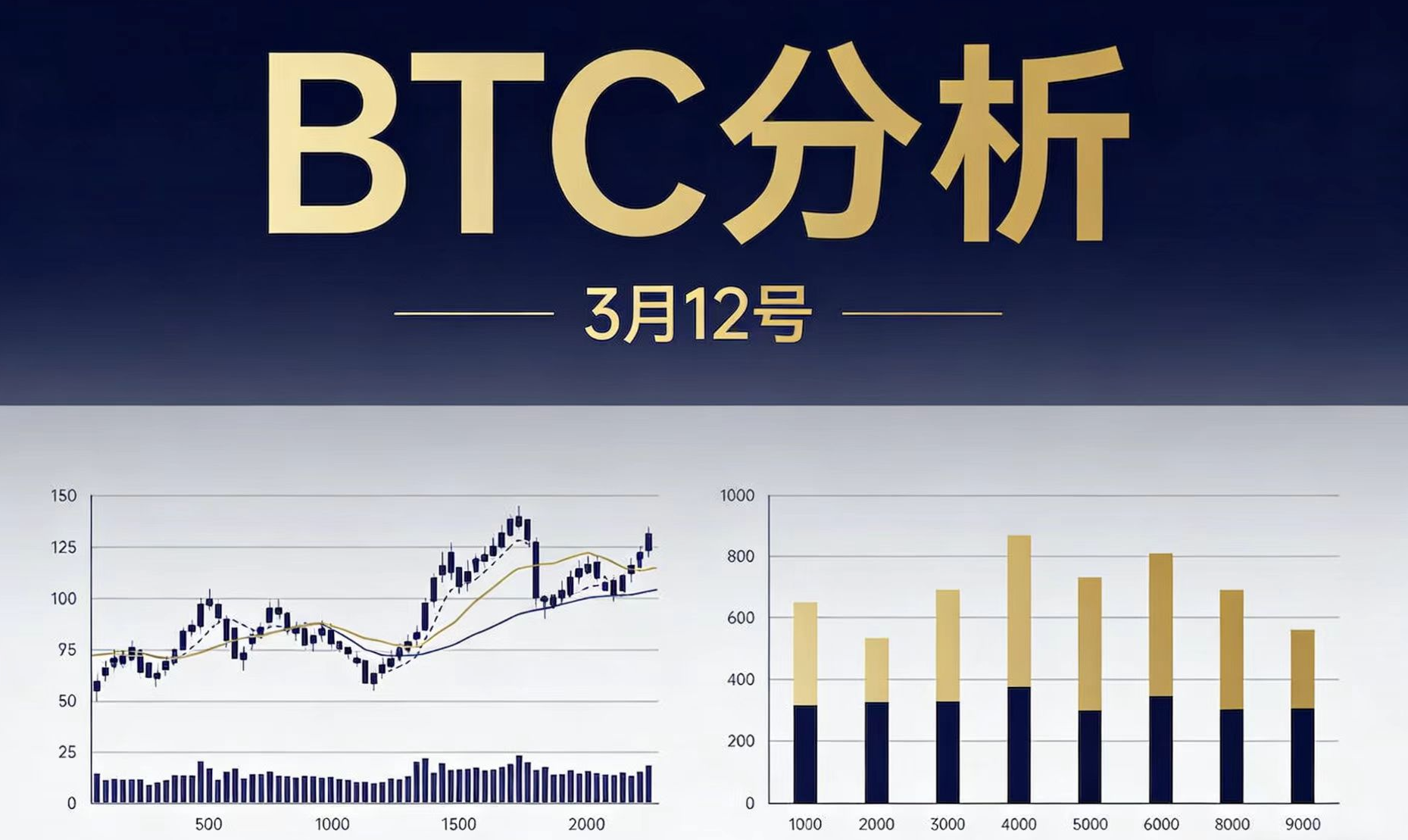
The Contrast Between Bitcoin and Ethereum ETFs' Fundraising and Entry Security
● Strong Fundraising of Bitcoin ETFs: During the same period when front-end security incidents like Bonk.fun were frequent, U.S. Bitcoin spot ETFs recorded net inflows for three consecutive days, with BlackRock's IBIT recording a single-day inflow of $115 million. This data shows that traditional financial institutions and compliant products are still continuously absorbing off-exchange funds, creating an investment channel relatively parallel to the on-chain world, dominated by custodians and exchanges, reshaping the way large capital enters.
● Supplementary Comparison of Ethereum ETFs: At the same time, U.S. Ethereum spot ETFs had a daily net inflow of about $57 million, with Fidelity's FETH performing particularly well, becoming one of the representative products in this wave of fund inflows. This expansion from Bitcoin to Ethereum ETFs further reinforced the path of "participating in crypto assets through traditional financial packaging," enabling mainstream funds to complete substantial allocations without touching the Web3 front end or operating on-chain wallets.
● Mismatch Between Fund Frenzy and Security Shortcomings: On one side, ETF products are consistently seeing inflows and scale steadily expanding, while on the other side, Web3 native entry points are frequently plagued by vulnerabilities—Bonk.fun is merely the latest example. This stark contrast exposes the structural misalignment in industry development: pricing, liquidity, and compliant packaging are rapidly maturing, while user experiences and security in directly accessing the on-chain world still remain in the "experimental field" stage, lacking the foundational infrastructure resilience that matches asset volumes.
● Focus and Neglect of Mainstream Funds: For most institutions and traditional investors, the focus lies on price performance, liquidity depth, product compliance, and custody security, while Web3 entry security is merely a faint background noise. They buy ETFs through brokerage accounts, rarely needing to open any dApp or connect unmanaged wallets. However, once some of these funds eventually flow into the native on-chain ecosystem, the security shortcomings of the entry layer will be magnified into a systemic risk, and this time lag is accumulating hidden dangers for the entire industry.
Regulatory Convergence and Trust Gaps in the Wake of SBF
● Formation of Regulatory Coordination Framework: At a macro level, the U.S. CFTC and SEC are collaborating to develop a regulatory coordination framework for cryptocurrency, aiming to delineate boundaries and unify standards between commodity and securities regulation. This progress signifies that the fragmented regulatory landscape of the past few years is being corrected, with market expectations about "what can be issued, how to issue, and who will regulate" gradually converging to a clearer trajectory, providing institutional support for compliant products and entities to enter.
● Long Shadow of the SBF Case: On the other hand, SBF's re-examination application faced opposition from the prosecution, and is currently serving a 25-year prison sentence. This conclusion has frequently been cited by media and regulators in public forums as a warning case of "disorderly expansion and internal loss of control." Although the collapse of FTX has become a thing of the past, its impact on the overall trust narrative in the industry is still ongoing, reminding the market that even in leading centralized platforms, trust can be destroyed in a short time.
● "Safer Yet Still Fragile" Psychological Structure: Stricter regulations, ETF approvals, and the judicial dust settling around major scandals collectively shape a complex market psychology: on one hand, investors feel that the environment is "safer" and "more predictable" than before, while on the other hand, new incidents repeatedly indicate that systemic vulnerabilities have never truly been far away. Incidents like Bonk.fun fall exactly into this subtle gap: they are not the black swan of compliance layers, but rather the gray rhino of technical implementation and entry management.
● Symbolic Significance of Bonk.fun in the Larger Context: If we place Bonk.fun in the wider context of "stricter regulations and trust restoration," we find its symbolic meaning far exceeds that of a single project incident. It indicates that even with the CFTC and SEC coordinating the cryptocurrency regulatory framework externally, and internally having SBF sentenced to 25 years as a cautionary example, as long as the entry layer still relies on centralized accounts and traditional domains, Web3 users remain exposed to old problems, and regulation and compliance cannot substitute for the absence of foundational security engineering.
Web3 Front-End Self-Rescue: From Single Entry to Multiple Safeguards
● Short-Term Response Template from the Incident: From Bonk.fun's response path, the primary measures that project teams can take in similar incidents include: immediately pausing entry guidance, issuing high-frequency risk announcements, and unifying messaging across all social platforms, prioritizing alerting users to disconnect and revoke suspicious authorizations. Although these actions cannot reverse the losses already incurred, they maximize the compression of additional victim numbers in the early stages, where information remains highly asymmetric.
● Engineering Practices to Reduce Single Points of Failure: Looking at the medium to long term, contingency plans for multiple domain names, signature prompt optimizations, and front-end open-sourcing are frequently discussed practical directions. By preparing backup domain names in advance, displaying clearer signature information in key operations, and opening front-end code in public repositories for auditing, it is expected to provide buffering space and external verification channels when accounts or a specific domain are hijacked, preventing all traffic from simultaneously rushing to a "polluted" channel.
● Exploration of Decentralized Hosting and Content Addressing: Further discussions focus on decentralized front-end hosting and access methods based on content addressing, such as utilizing distributed storage networks or on-chain registered entry information to weaken the dominance of DNS and traditional servers. However, research briefs also indicate that relevant directions are still under community exploration with no unified implementation path, and that uncertainties exist in compliance and user experience, so it can currently only be regarded as a frontier experiment rather than an industry conclusion.
● The Final Link in User Side Security Habits: Regardless of how front-end engineering evolves, security habits on the user side remain an irreplaceable component. This includes: always verifying link sources from official channels, avoiding accessing critical applications via search ads, carefully checking authorization content and amounts before each signature, and adhering to the "least authorization principle" instead of one-click unlimited authorization, among others. Only when project teams and users build up multi-layer defenses together, can the vulnerabilities of the entry layer be gradually weakened.
The Entry Battle Is Not Over: Funding Frenzy and Security Boundaries Reshaped
In the Bonk.fun domain hijacking incident, we see a clear fracture: on-chain asset protection measures are becoming increasingly mature, while the entry layer remains in a Web2 paradigm that is easy to breach. This gap violently strips apart the "right to own assets" and the "ability to safely reach those assets." As long as domains can be controlled and front-ends can be replaced, any discussion about the security of decentralized assets remains incomplete.
Against the backdrop of continuous net inflows into Bitcoin and Ethereum ETFs, IBIT's single-day inflow of $115 million, and Ethereum ETF's single-day net inflow of $57 million, cryptocurrency assets are being allocated by mainstream funds at an unprecedented speed; meanwhile, events like CFTC and SEC accelerating regulatory coordination and SBF serving a 25-year sentence are also reshaping the industry's compliance profile. Going forward, Web3 front-end and entry security are likely to become a new battleground of focus shared by regulatory, infrastructure teams, and large funds, rather than merely a niche topic for tech enthusiasts.
For individual users and institutional participants, what truly needs to be re-evaluated is "how much trust am I placing on a centralized entry." As we pursue new narratives and high returns, are we also consciously diversifying entry risks, establishing backup access paths, and adopting safety habits? In the coming years, more mature decentralized front-end tools and clearer compliance frameworks are expected to reshuffle the security boundaries of Web3 through continuous collision and integration, ensuring that “mastering private keys” and “safely entering the chain” are no longer separated by a fragile domain threshold.
Join our community, let’s discuss together and become stronger!
Official Telegram community: https://t.me/aicoincn
AiCoin Chinese Twitter: https://x.com/AiCoinzh
OKX benefit group: https://aicoin.com/link/chat?cid=l61eM4owQ
Binance benefit group: https://aicoin.com/link/chat?cid=ynr7d1P6Z
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。