Written by: Lacie Zhang, Bitget Wallet Researcher
Abstract: In 1984, Apple killed the command line with a mouse. In 2026, Agents are killing the mouse.
In 1984, Apple (Macintosh) killed the command line with a mouse. In 2026, Agents are killing the mouse.
This is not a metaphor. Companies that have spent billions of dollars refining graphical interfaces, such as Google, Amazon, Nvidia, Visa, Microsoft, and Alibaba, are actively bypassing GUIs and moving towards CLI, APIs, and Agent native interfaces. The logic is simple: human-driven growth from 0 to 1 relies on people, but the next tenfold user base will no longer look at screens.
But what everyone is avoiding is: when the users of software change from humans to Agents, do humans still need to be present?
As early as 1950, Norbert Wiener, the founder of cybernetics, warned that once humans lose the ability to observe and intervene, feedback loops will break, and systems will spiral out of control. Today, what OpenAI emphasizes as "Harness Engineering" is essentially a continuation of this idea.
More than seventy years later, Agentic Wallet faces a cryptographic version of this question. Confirmation pop-ups, signature requests, approval processes, mnemonic backups, multi-factor authentication... the security mechanisms that have taken a decade to build in crypto wallets are all answering one question: "Is this operation really authorized by you?" Agents are making this human interaction mechanism begin to fail: continuing to require manual confirmation for each transaction makes it impossible for Agents to execute continuously, in real-time, and automatically; directly handing over the boundless control of private keys to Agents leaves humans with unacceptable risks.
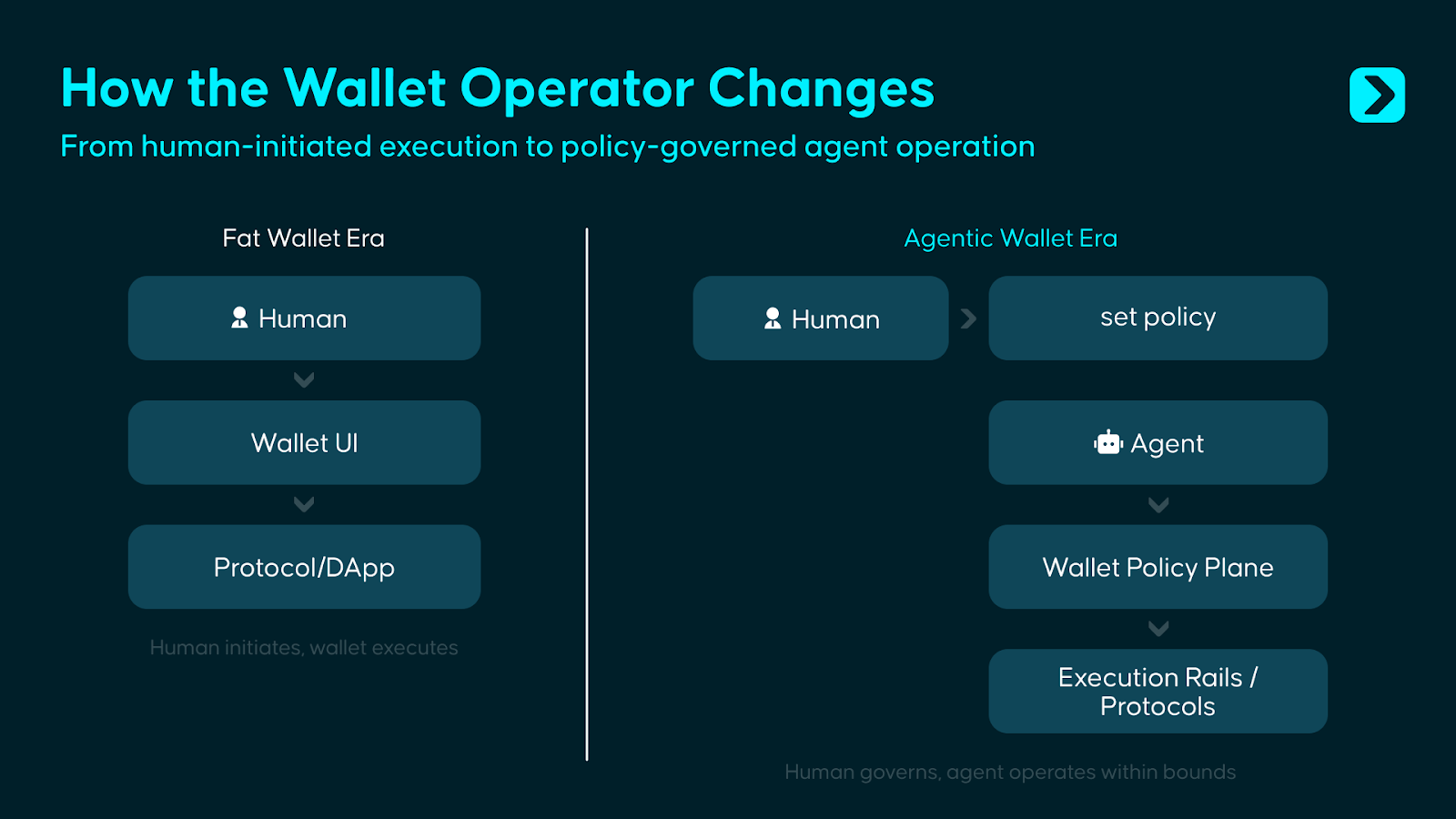
The answer does not lie at either extreme. Complete autonomy is the most attractive narrative of the Agent era, but Wiener’s warning still holds. We believe that the Agentic Wallet must serve two types of entities simultaneously: on one hand, it provides humans with the ability to set rules, control risks, and intervene in governance; on the other hand, it grants Agents constrained execution permissions, allowing them to autonomously complete on-chain operations within clearly defined boundaries. In other words, the wallet needs to evolve from a container for assets and a signature tool for human use into a control and execution system that allows humans to set boundaries and Agents to operate within those boundaries.
What should this system look like? This is the question this article aims to answer.
1. Beyond Fat Wallet, Another War for Wallets
Delphi Digital proposed a powerful judgment in the Fat Wallet Thesis: As protocols and applications become increasingly homogeneous, value will settle at the wallet layer because wallets are closest to users, controlling distribution channels and order flows, and users will linger in a particular wallet due to familiar interfaces, accumulated assets, and migration friction.
However, Agents do not follow the same logic. As "unfeeling" machine executors, Agents will not remain in a particular wallet due to familiarity with the interface, brand preference, or usage habits; they will continuously seek the lowest cost, least delay, and most stable infrastructure combinations. With the gradual popularization of standards like ERC-8004, the identity and reputation layer of Agents may also be expected to migrate across different systems, meaning the locking effect of wallets on Agents is inherently weaker than on humans.
However, this does not mean that the value of wallets disappears; rather, the location of value deposition will change. In simple personal use scenarios, Agents will weaken the original moat of wallets formed based on interface, habits, and access; while in relatively complex organized deployment scenarios, once enterprises configure strategy rules, approval processes, risk control parameters, and audit systems around an entire "Agent fleet," the migration costs will henceforth derive not from the front-end experience, but from the reconstruction of the entire set of permissions, governance, and operational configurations.
Therefore, the Agentic Wallet addresses another proposition outside of Fat Wallet: Fat Wallet competes for user access, while Agentic Wallet competes for control when software begins to directly manage funds.
If we look back at the evolution of wallets, we can see that each change in product form corresponds to a shift in user trust objects:
- Mnemonic wallets require users to trust themselves.
- Smart contract wallets require users to trust the code.
- Embedded wallets require users to trust the service provider.
- And with the Agentic Wallet, what users need to trust is a control system composed of permissions, policies, and governance mechanisms.
The goal of this system is not to allow software to take over funds, but to enable software to operate under limited authorization while ensuring that humans retain final control. Therefore, the core of the Agentic Wallet is not just "enabling Agents to use wallets," but rather "allowing Agents to manage funds belonging to human users under conditions that are constrained, auditable, and intervenable."
2. The Boundaries of Wallets, the Starting Point for Agents
Current wallets still operate well within the scenarios for which they were originally designed, but the problem is that an increasing number of Agent-driven use cases are surpassing the design boundaries of existing wallets.
Scenario 1: Trading Agents need to act quickly, but "having the ability to execute" does not equal "being allowed to execute."
A portfolio Agent monitors cross-chain liquidity around the clock. When an opportunity arises, it needs to complete a transaction within seconds. The control logic of traditional wallets is for users to open the app - check the transaction - click confirm. By the time this whole process is completed, the opportunity window is often closed.
Technically, Agents already have the capability to call the swap function, generate calldata, and bridge funds; the problem is that ability does not equal permission. Just because an Agent can initiate a transaction does not mean it should be allowed to freely manage funds.
The role of Agentic Wallet is precisely to separate the two: Agents can act instantly but only within preset rules, such as limited to approved assets, bounded by daily budget limits, constrained by slippage limits, and automatically pausing in abnormal market conditions. Skills define what Agents "can do," while the wallet constrains what Agents "are allowed to do."
Scenario 2: Payment Agents need to spend money but should not have full control over all funds.
A payment Agent is responsible for automatically settling API bills, SaaS subscription fees, and vendor payments. In the current wallet system, it typically has two options: either wait for human approval for each payment or hold a private key with unlimited signing rights. The former is not scalable, while the latter carries excessive risk.
Agentic Wallet offers a form of limited authorization: it can only pay whitelisted merchants, can use specified assets, can execute payments within the daily budget, and all expenditures are fully recorded.
Scenario 3: Multiple Agents need to have isolated permissions under a shared budget.
One entity may run multiple Agents simultaneously: one for trading, one for payments, and one for reviews. Current wallets can create multiple sub-accounts, but coordinating permissions for these accounts, setting global budget limits, executing cross-Agent policy constraints, and forming unified audit trails is not a native capability of existing wallets.
Under the Agentic Wallet model, this would be treated as a prioritized design issue: each Agent has its own independent, clearly defined permissions; at the same time, a unified policy layer is responsible for controlling overall risk exposure, cross-Agent frequency limits, shared budgets, and generating consistent audit records.
These scenarios point to the same conclusion: private key management remains the foundation of wallet security, but allowing Agents direct access to private keys is an unacceptable source of risk in any scenario. However, merely managing private keys is no longer enough. As operators shift from humans to Agents, wallets must also address a second question: who is allowed to act under what conditions, with what limits, on which assets, and towards which targets? Private key management is the first line of defense, while permission boundary management for non-human operators forms the second new firewall in the Agent era.
3. Bounded Autonomy: The Design Philosophy of Agentic Wallet
The industry is still in the early exploratory stages regarding Agentic Wallet, and there is not yet a truly mature Agentic Wallet solution. However, as mentioned in the introduction, what this article considers an Agentic Wallet is a funding control system that connects human governance and Agent execution: humans are responsible for setting boundaries, Agents for acting within those boundaries, and wallets for ensuring that this constraint relationship is always executable, auditable, and intervenable.
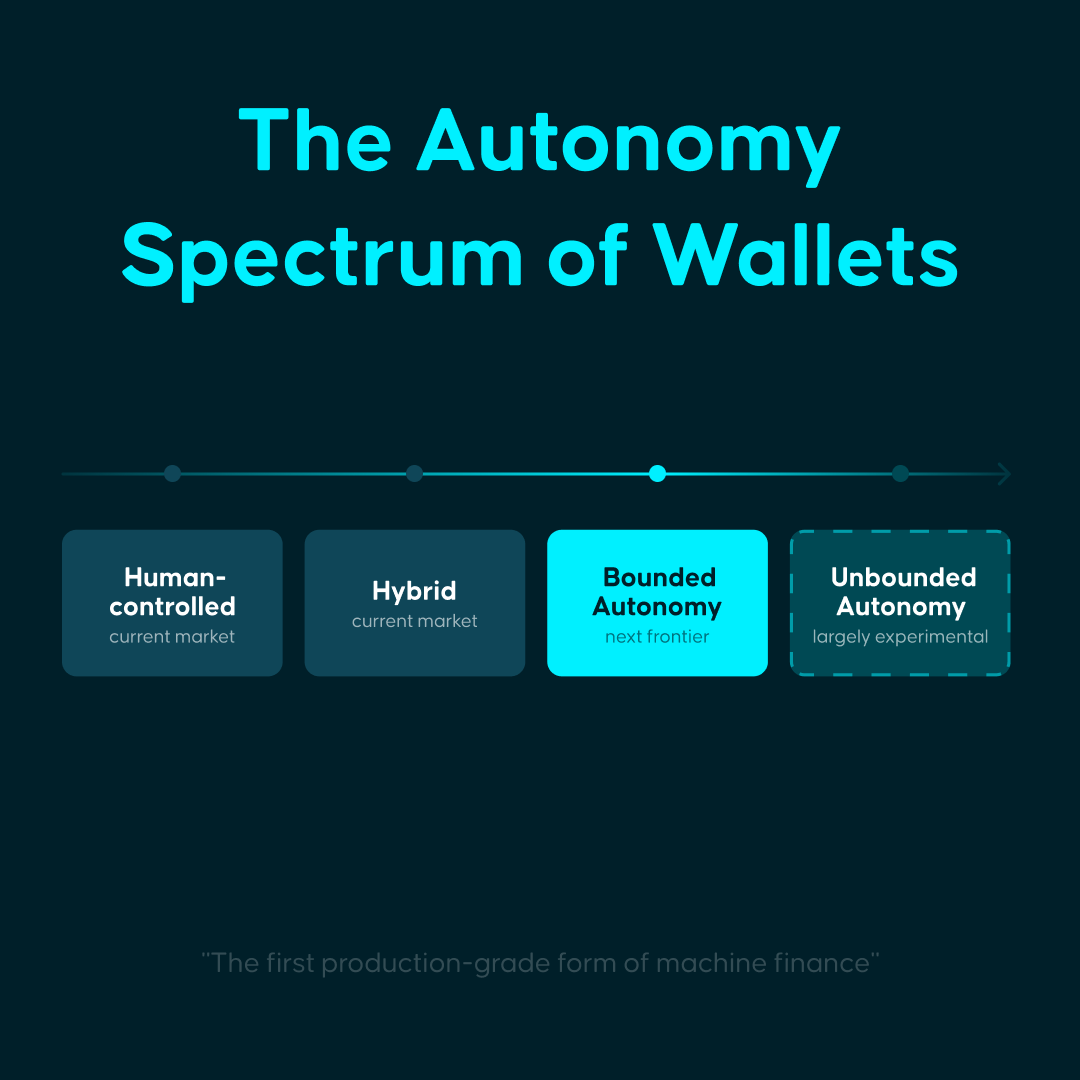
According to the degree of authorization obtained by Agents, the Agentic Wallet may also serve the following four situations:
- Human-controlled: Agents provide suggestions and assistance, but each operation still requires human confirmation. The interaction efficiency is improved, but the logic of fund control remains unchanged.
- Hybrid: Agents handle routine operations, such as retrieval, quoting, reminders, or low-risk execution; the frequency of human intervention decreases, but boundary situations still require human approval, such as for fund transfers, contract calls, or exceptions.
- Bounded autonomy: Agents act autonomously within explicit rules, limits, and veto paths. Humans transform from transaction approvers to rule setters. The Agentic Wallet discussed in this article mainly refers to this category.
- Fully autonomous: Agents possess near-complete economic sovereignty, able to independently allocate funds without preset boundaries and assume the results. This model is theoretically valid but remains immature in terms of security, governance, accountability, and compliance, currently mostly staying at the experimental stage.
For reference, Stripe, in its 2025 annual letter, classified agentic commerce into five levels: L1 for filling out forms (Eliminating web forms), L2 for descriptive search (Descriptive search), L3 for persistent memory (Persistence), L4 for delegated authorization (Delegation), and L5 for anticipative purchasing (Anticipation); it also clearly judged that the industry overall is still "hovering at the edge of L1 and L2."
From this perspective, the largest market demand currently may come from human-controlled and hybrid scenarios, while bounded autonomy is the current frontier and the first production-grade form where Agents truly begin to manage funds.
Realizing this vision requires a four-layer architecture:
- Account layer: Establish independent, isolated economic containers for each Agent, such as through EOA, smart contract accounts, server wallets, or TEE environments. The system needs to impose differentiated rules on different Agents.
- Permissions layer: Define the behavioral boundaries of Agents, such as dispensible amounts, operable assets, interactable contracts, executable time windows, and action logic after touching boundaries. This is the core layer of the entire architecture.
- Execution layer: Focused on Agent interfaces rather than human clicks. Sending, paying, swapping, bridging, rebalancing, clearing, and settling all need to be abstracted as primitives that can be called directly by programs.
- Governance layer: Needs to provide logs, simulations, audit tracking, alerts, pause switches, human veto rights, recovery mechanisms, and so on. This layer determines whether the Agentic Wallet can truly enter the production environment.
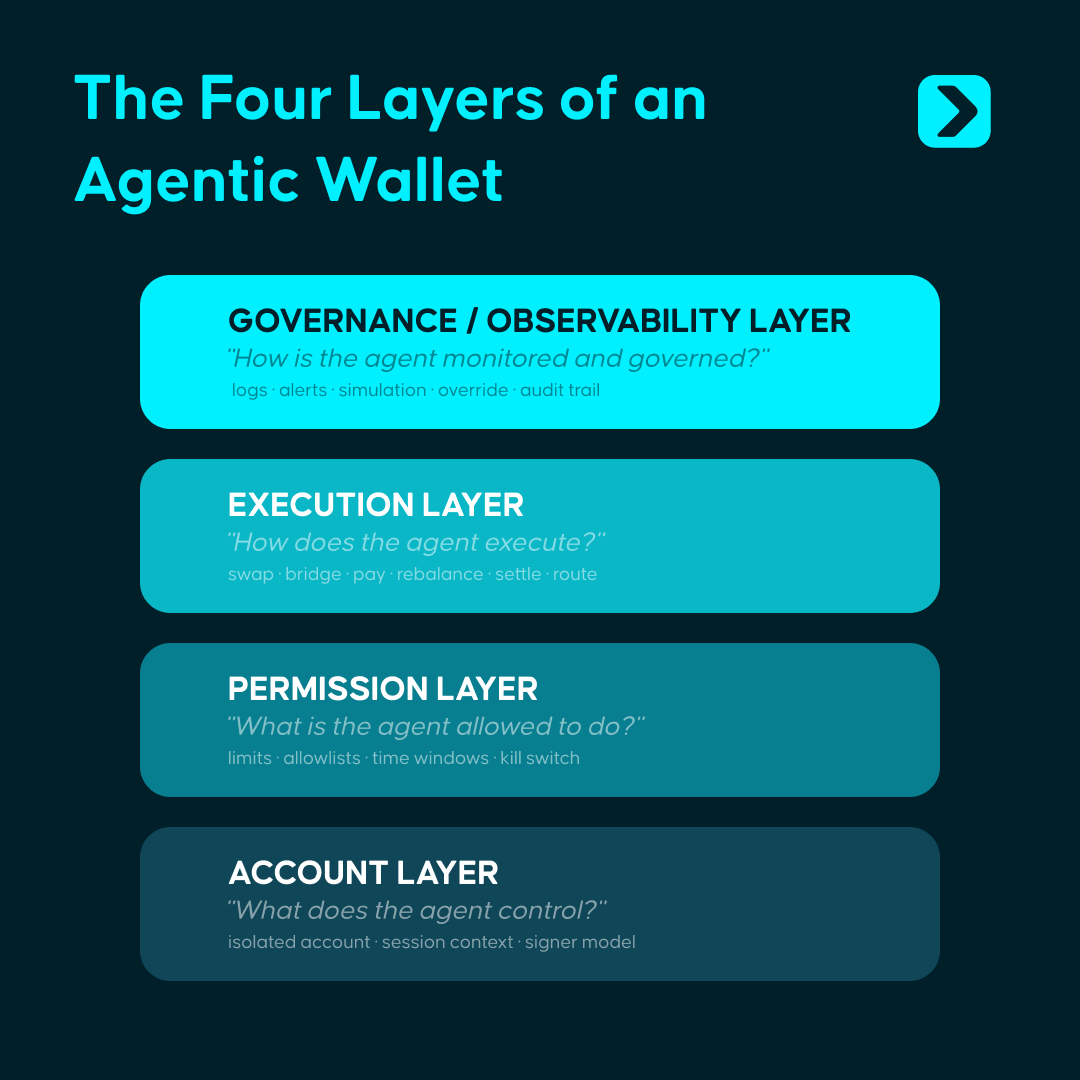
Above the four-layer architecture, there are also four core capabilities required to support system operation:
- Skills: Provide standardized on-chain operation modules. Agents can complete actions such as trading, paying, bridging, etc., like calling functions, without assembling the underlying calldata themselves. Skills solve the capability abstraction problem of "what can be done."
- Policies + KYA / KYT: The Policies engine is responsible for validating the rules of each operation, converting the boundaries set by humans into machine-executable constraints; KYA/KYT mechanisms are used to identify the source, identity, risk context, and operational history of Agents. The former constrains behavior, while the latter identifies operators; together, they ensure that all funding actions always remain within preset boundaries.
- Session Key: Provide a secure delegation mechanism with time-limited, amount-limited, and range-limited authorizations. Agents obtain temporary and limited authority rather than full private keys. Authorization expires automatically without manual revocation, "allowing Agents to gain execution qualifications without accessing the complete key."
- Audit and notifications: Provide fully traceable operation logs and real-time alert systems. Each operation is traceable, each anomaly can trigger alerts, and each Agent can be paused at any time.
Currently, we typically control the behavior logic of Agents through instructions, but task orchestration does not equate to funding constraints. Agents can still misjudge, deviate, or suffer from attacks and malicious input contamination. The significance of the wallet layer lies in pre-setting system rules for issues related to funding permissions such as "whether funds can be utilized, how much can be used, which assets can be operated on, which objects can be interacted with, and how to halt in abnormal situations." Even if Agents deviate, any funding actions that can actually occur are still restricted within preset boundaries.
4. The Current State of Agentic Wallet: Four Paths and Four Gaps
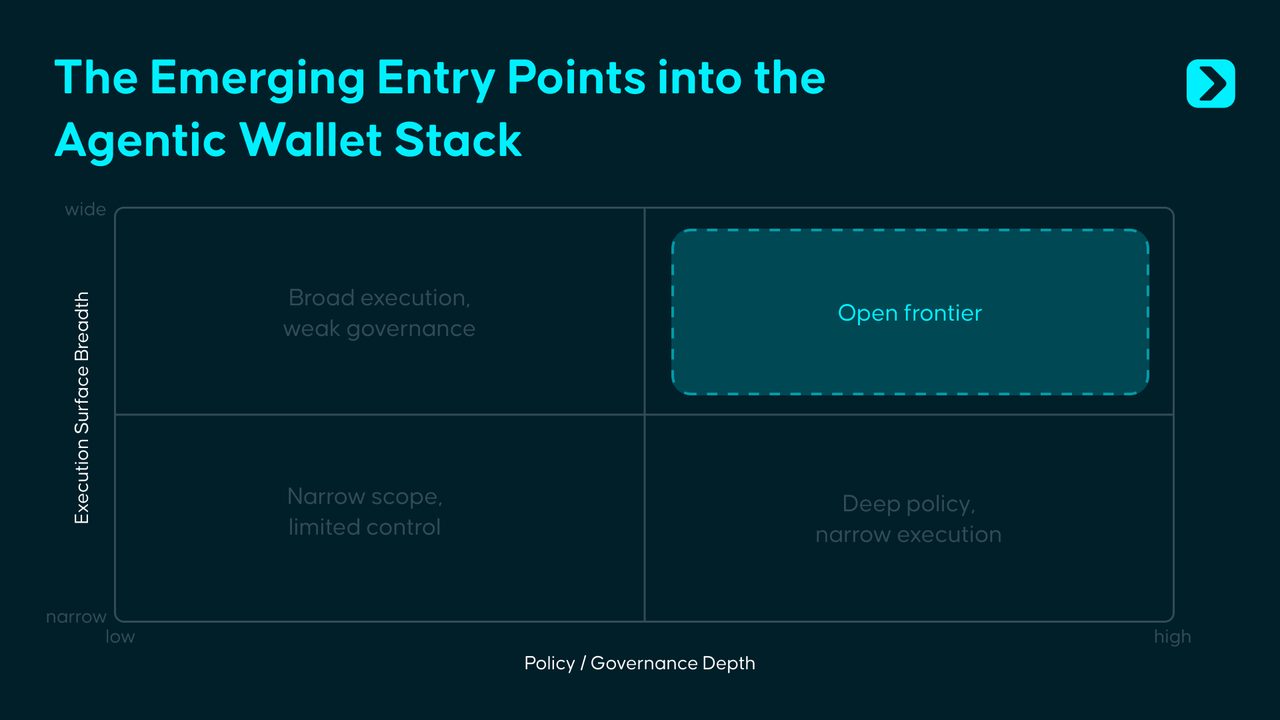
Surrounding the existing Agentic Wallet solutions, we have identified four typical cases that have basically resolved the question of "how to allow Agents to enter the funding system," but have yet to answer "how to enable Agents to safely use funds in cross-chain and complex real-world environments."

Coinbase, Safe, Privy, and Polygon have each provided viable answers at the infrastructure, governance, permissions, and identity levels. What remains unfinished is integrating these localized capabilities into a unified control system that can operate across chains, migrate across environments, and still hold valid in complex adversarial scenarios. The common bottlenecks of the current Agentic Wallet are mainly concentrated in the following four gaps:
Firstly, identity and reputation are not yet transferable.
On-chain Agent identity and reputation systems can be established, but a universal credit system that works across chains, wallets, and operating environments does not yet exist. The history and reputation that an Agent accumulates in a particular ecosystem cannot naturally migrate to another ecosystem.
Secondly, the strategy layer lacks a unified standard.
Coinbase uses spending limits, Safe uses on-chain modules, Privy uses policy engines, and Polygon uses session-scoped wallets. The industry has generally recognized that the permissions layer is core, but a unified strategy standard that is portable, composable, and cross-product reusable has not yet formed.
Thirdly, adversarial security remains highly blank.
Prompt injection, tool poisoning, malicious skills, contaminated external inputs, these issues will not be automatically resolved by traditional contract audits. The truly new problem in the era of Agents is: how does the wallet identify, intervene, and block risks when the decision-making process of a model is distorted by malicious input?
Fourthly, full-chain coverage is far from achieved.
Existing solutions mostly rely on single chains or limited multi-chain scopes, but the economic activities of Agents will not remain long in a single ecosystem. A truly mature Agentic Wallet must contend with issues of multi-chain, multi-execution environments, and cross-domain permission consistency.
5. Below the Surface: The Next Decade of Agentic Wallet
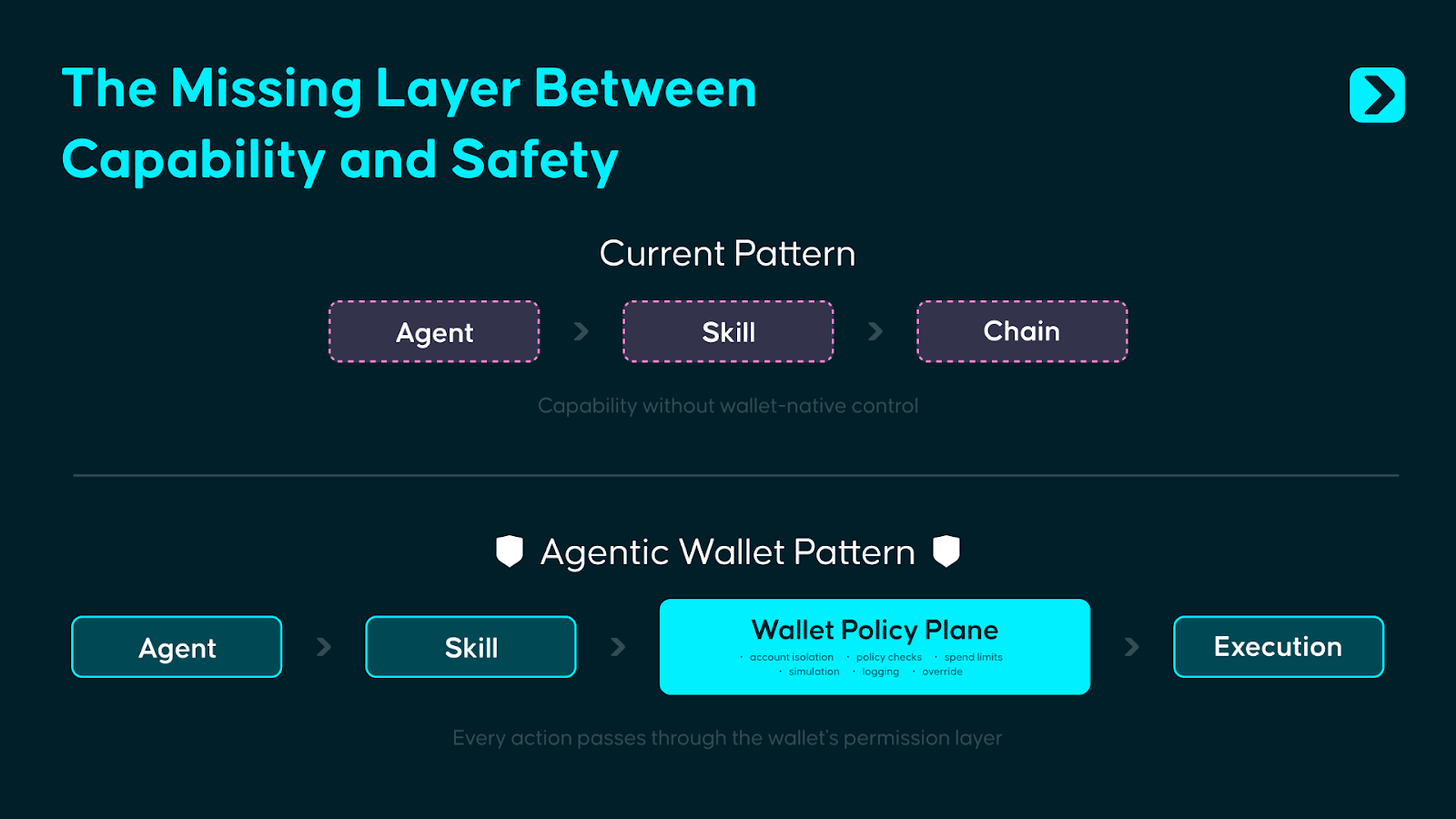
Currently, the design focus of Agentic Wallet is to empower humans to impose refined controls on Agents. In most implementations, the wallet's role is closer to that of a passive signer: Agents invoke Skills, Skills generate transactions, and the wallet completes the signature in the backend, leading to on-chain execution.
However, if Agents truly begin managing funds, simply signing at the last step is clearly insufficient. A more reasonable approach is to ensure that permission judgments occur before execution: after an Agent invokes a Skill, the request should first enter the wallet's internal Policy Plane, and only through policy verification can the execution be authorized.
The so-called Wallet Policy Plane borrows from the concepts of Control Plane and Data Plane in system architecture. It lies between the behavior of Agents and on-chain executions, integrating the Policies engine, KYT/KYA verification, Session Key validation, risk scoring, and anomaly handling into a unified decision-making plane.
This idea is not unfamiliar; Stripe's payment architecture operates under a similar logic: developers call a clean API, but before funds actually move, Stripe has backend mechanisms for risk identification, rule checks, and compliance processing. The task of the Agentic Wallet is essentially the same, providing a clean execution interface to developers while using a front-end policy engine for authorization decisions.
The urgency lies in the fact that the attack surfaces brought about by prompt injections, tool poisonings, and malicious skills are rapidly expanding, while the security infrastructure on the wallet side has not kept pace. A standardized Wallet Policy Plane has not yet become a common foundational primitive in the industry.
However, the Policy Plane itself will not represent the final state. As the identity and reputation systems for Agents gradually mature, authorization logic will shift from being static rule-driven to dynamic trust-driven. Today, it relies on preset boundaries, amount limits, whitelists, and manual veto paths; in the future, on-chain transaction records, behavioral trajectories, and cross-ecosystem credit data will gradually form a verifiable foundation of Agent credit, with more authorization decisions made based on identity, history, and actual performance.
When Agents begin economic interactions with each other at machine speed, the control mechanisms must be built-in from the outset of the system's establishment. The role of the wallet will also change: in the early stages, it acts as a gatekeeper, responsible for preventing boundary violations; in the mature stage, it becomes closer to infrastructure, responsible for enabling trusted entities to continually connect accounts, permissions, and settlement systems with lower friction.
In the past decade, the battlefield for wallets was that entry point on screens. In the next decade, the battlefield will be the layer of control that users cannot see.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



