Written by: Glendon, Techub News
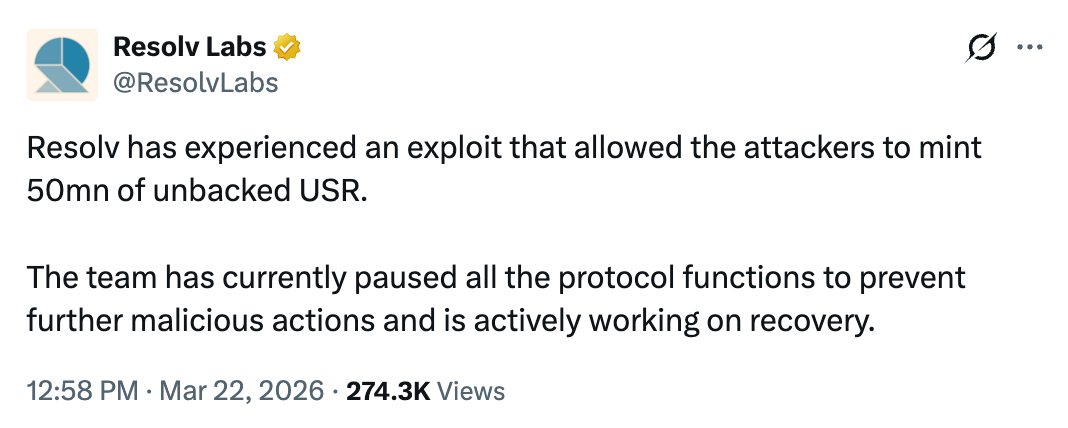
On March 22, Resolv Labs, a developer focused on creating decentralized interest-bearing stablecoins, suffered a hack. On-chain data showed that an attacker address starting with "0x04A2" deposited only 100,000 USDC but exploited a protocol vulnerability to mint 50 million USR stablecoins. Subsequently, the attacker used another 100,000 USDC to mint 30 million USR again. During this period, Resolv Labs officially confirmed via Twitter that the protocol had been attacked, stating that the team had suspended all protocol functions and was working on recovery.
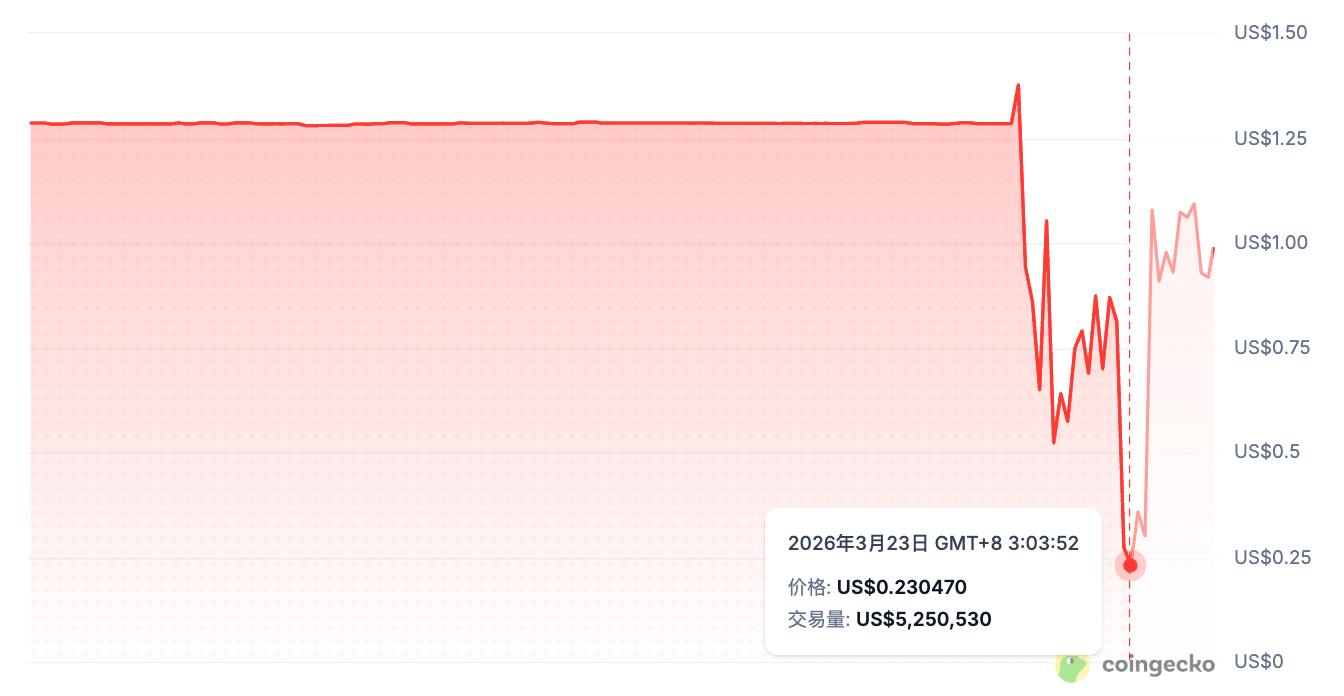
However, it was too late. A total of 80 million USR, which had no asset backing, had already flooded the market, causing the stablecoin USR to quickly de-peg. At the same time, due to market liquidity drying up, severe slippage occurred during trading executions, further exacerbating the decline of USR. Data from CoinMarketCap showed that USR once de-pegged to about $0.06, a drop of over 94% (current USR has rebounded to about $0.32 but remains in a "serious de-pegging" state). Notably, the attacker’s cash-out path was clear and rapid, completing the entire process within a few hours. They converted the illegally minted USR to wstUSR and heavily sold it on decentralized exchanges like Curve and Uniswap, exchanging it for USDC and USDT, before converting these stablecoins into Ethereum worth about $25 million, successfully completing a "lightning raid" to launder the attack profits.
In the current already sluggish market environment, the attack on Resolv Labs undoubtedly dealt another blow to industry confidence, even being referred to in the crypto community as a "classic script" of the bear market. The reason for the attack remains the often-discussed issue of "minting mechanism design flaws."
Vulnerability Source: Triple Failings in the Minting Mechanism
First, it is important to clarify that Resolv's stablecoin system employs a two-tier structural design. USR is a stablecoin pegged 1:1 to the US dollar, and users can mint USR by depositing ETH or BTC. It utilizes a delta-neutral strategy, allowing the protocol to open equivalent short perpetual positions for held ETH/BTC to hedge against price volatility risks, thereby keeping USR stable. Meanwhile, USR holders can earn a portion of the protocol's generated revenue and further participate in yield aggregation within DeFi protocols like Pendle and Sommelier.
At the same time, Resolv introduced the Resolv Liquidity Provider Token (RLP) to serve as the system’s "insurance pool," used to absorb potential losses in hedging strategies due to liquidation, slippage, and funding rate fluctuations. In this attack, RLP was not spared. According to Coingecko data, RLP's price also dropped from $1.38 to $0.23, a decline of over 83%. Currently, RLP has rebounded to $0.98.
So, how did Resolv Labs fall victim to a hack? Comprehensive security company PeckShield and several on-chain analysts analyzed that the root cause of the Resolv Labs hacking incident lies in serious design flaws in the minting contract's permission control and verification mechanisms. First, there is a critical flaw in permission control. Under normal circumstances, users must deposit the corresponding collateral to mint USR, and the minting quantity should be tied 1:1 to the collateral value. However, attackers exploited SERVICE_ROLE permissions to bypass the collateral value verification step, directly setting the minting amount to an astronomical figure, thereby achieving "super high leverage" by minting 80 million USR with only $200,000 USDC.
This design flaw is that SERVICE_ROLE has the power to directly determine the minting quantity, representing "super permissions." Since the protocol did not adopt multi-signatures or a decentralized signer network, but relied on a single or a few signers, once the keys were leaked or compromised, the system would immediately fail.
Secondly, the lack of on-chain amount verification mechanisms poses a significant security risk. Resolv Labs' minting contract fully trusts the minting quantity provided by off-chain signers, has neither set an on-chain amount limit (such as a maximum of 1 million USR per transaction), nor introduced oracles to perform real-time verification of collateral value and minted quantity. This means that as long as the attacker controls the off-chain signer or gains the respective permissions, they can freely mint USR without regard for whether the collateral is sufficient. It was this lack of verification that opened the door for the hacker attack.
Thirdly, there are potential risks in the delta-neutral strategy. Resolv Labs adopted a delta-neutral strategy to issue USR, but this incident also revealed design weaknesses of this strategy. The delta-neutral strategy tightly couples the protocol's minting logic with off-chain signatures and oracles, and these coupling points happen to become the most vulnerable attack surfaces of the system. Once the off-chain signer or oracle has issues, the entire minting mechanism may fall into chaos.
Early this morning, Resolv Labs finally published a statement detailing the cause of the attack. The incident stemmed from unauthorized third-party actions, including targeted infrastructure intrusions and cyberattacks. The attacker accessed Resolv's infrastructure through leaked private keys, leading to about $80 million of uncollateralized USR being illegally minted.
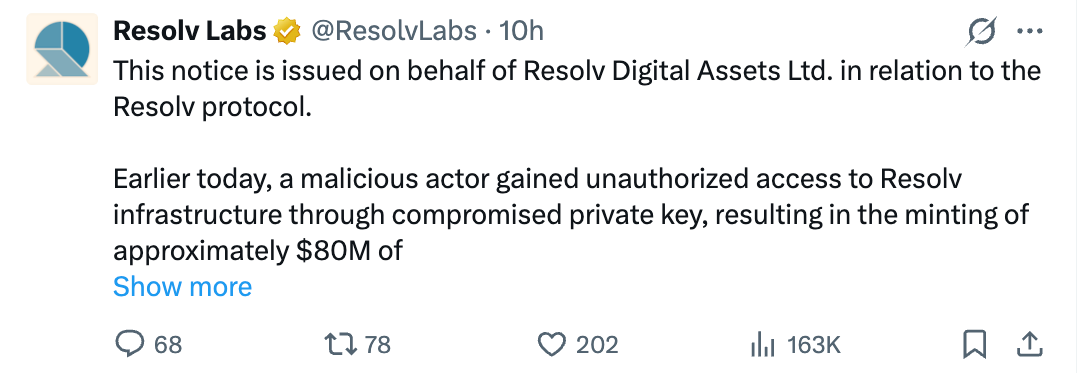
At the same time, Resolv Labs disclosed that about 9 million USR held by the attacker has been successfully destroyed. The current USR supply includes 102 million USR that existed before the incident and about 71 million new illegally minted tokens. In an effort to recoup losses and restore normal order, they are preparing to enable the redemption function for USR that existed before the attack today, starting with whitelisted users. They once again emphasized that the underlying collateral assets of Resolv were not directly affected, and they are tracking and trying to control the illegally minted USR and other affected assets.
This move is Resolv Labs' initial remedial measure for early users, showing that the company is working hard to mitigate losses and recover lost funds. However, this incident has already caused a chain reaction in the industry.
Chain Reaction and Implications
The most direct impact of the Resolv Labs incident is undoubtedly the severe de-pegging of USR and the price drop of the native token RESOLV. RESOLV once fell over 16% to $0.052. Additionally, many DeFi protocols were affected. The USR/USDC liquidity pool on Curve Finance instantly collapsed; the lending market in Morpho that supported USR and wstUSR as collateral was almost completely cleared, with many users facing forced liquidation risks due to USR's de-pegging.
However, Morpho co-founder Paul Frambot tweeted today that the impact of the Resolv Labs attack on Morpho is not as significant as rumored. The incident mainly affected USR and related assets (such as RPL), as well as the lending market using these assets as collateral. Among approximately 500 vaults with deposits exceeding $10,000, about 15 vaults had significant exposure to the affected market (over $10,000).
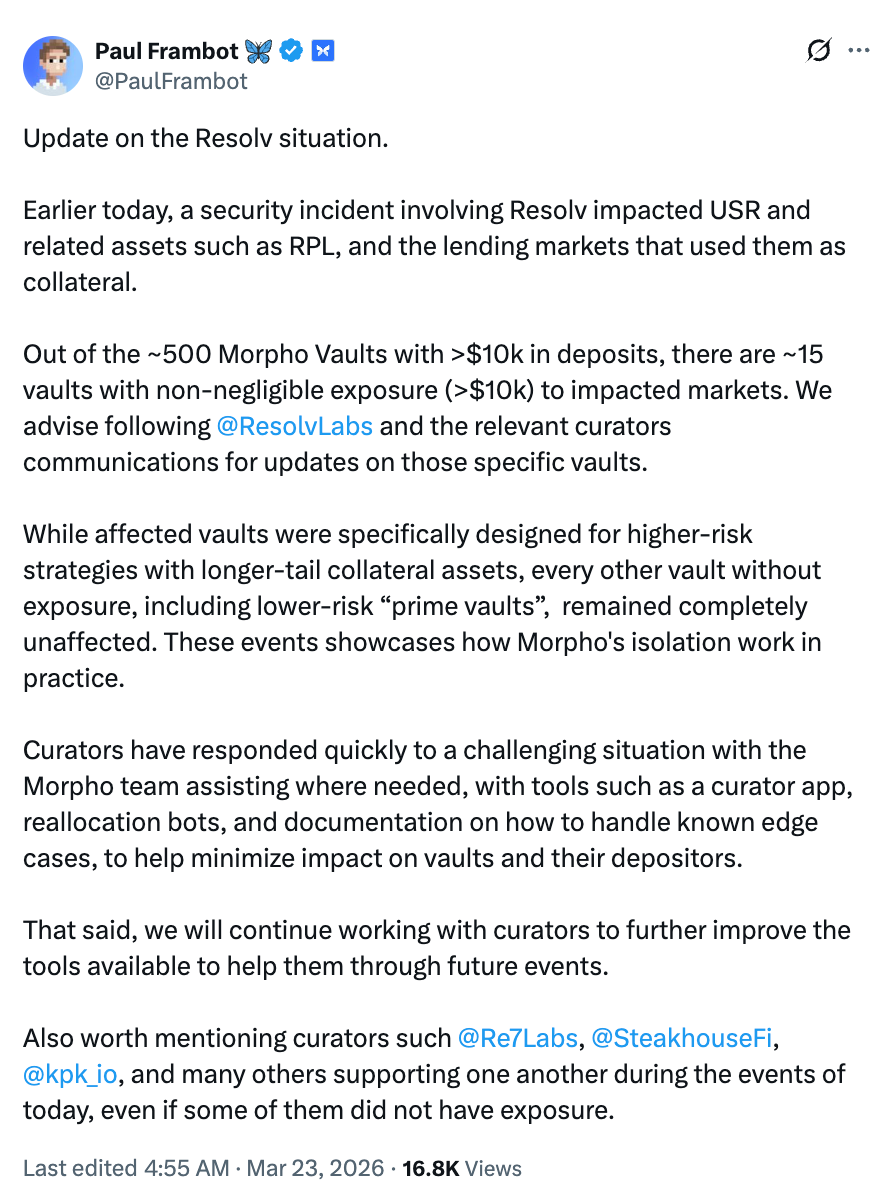
Moreover, although other protocols or ecosystem partners integrated with Resolv did not suffer major impacts, they were still forced to take emergency measures to protect their users. For instance, the DeFi risk management protocol Gauntlet emphasized that Gauntlet USD Alpha does not hold USR or RLP positions, and its vaults on the platform are unaffected; funds providers are also not affected, and it is discussing solutions with Resolv. For remaining funds, Gauntlet is devising a compensation plan.
The DeFi protocol Fluid stated that its team has secured a short-term loan to cover all current bad debts in the protocol, ensuring user funds' safety. Aave founder Stani.eth also tweeted that his protocol has no exposure to Resolv Labs' stablecoin USR, noting that Resolv only acted as a liquidity provider to supply its supporting assets to the Aave protocol, and all related assets are currently secure. Other protocols that use USR as a yield-earning asset for yield aggregation (like Pendle and Sommelier), although not directly incurring losses, also saw indirect impacts on yield rates and asset values in their related pools.
This again reveals a harsh reality in the DeFi ecosystem: the failure of one protocol could trigger a "chain collapse" of multiple protocols, especially when a particular asset is widely used as collateral. Even if these protocols were not directly attacked, they could still suffer reputational and operational collateral damage from risk events related to associated projects.
Moreover, during the event, the attacker sold the illegally minted 80 million USR in batches into the USR/USDC liquidity pools on DEXs like Curve and Uniswap, causing sharp price fluctuations. Due to the collapse of USR's value, liquidity providers faced not only "impermanent loss" but also substantial capital losses because the assets they ended up holding were nearly all de-pegged USR. This phenomenon also exposed structural weaknesses in emerging asset liquidity pools (those with low trading volumes or insufficient depth) that lack adequate trading depth to absorb massive sell pressure, leading to instant price distortion and rapid spreading of systemic risk.
From a broader perspective, the Resolv Labs incident is not just a simple security breach of a single project but also another severe blow to investor confidence in the crypto market, potentially triggering a new round of stablecoin trust crisis. Stablecoins, being fundamental to DeFi activities, their de-pegging and security issues often shake the foundational stability of the entire ecosystem, leading the market to have deeper doubts about the long-term viability of "algorithmic stablecoins" and "interest-bearing stablecoins." It could even lead some risk-averse investors to begin withdrawing from high-risk DeFi protocols and shifting towards more mature assets or hedging strategies.
This incident undoubtedly serves as a warning bell for the entire industry, especially in the current crypto market that remains in a bear cycle and where risk appetite is generally low, its warning significance is further amplified. The issues of "over-reliance on off-chain signers without on-chain verification" exposed once again by Resolv are seen in the industry as a "collapse of trust models." At the same time, it also prompts more protocols to adopt multi-signature mechanisms to decentralize permissions, introduce decentralized oracle networks like Chainlink and Pyth for on-chain real-time verification, and embed automated circuit breakers to enhance the system's security and risk resistance capabilities.
Additionally, in terms of emergency response, from 10 a.m. to 12 p.m. yesterday, the Resolv team had only suspended the protocol more than two hours after the attack occurred, fully exposing the sluggishness of their emergency process. After this incident, the project should place greater importance on establishing a fast, automated crisis response system.
Conclusion
As of the time of writing, Resolv Labs has not yet announced a comprehensive compensation plan. There has been no clear compensation plan disclosed for users who held USR during the attack or suffered losses due to de-pegging, as well as for RLP token holders due to the dilution of the insurance pool's value. The market is also closely watching whether they will provide further compensation to the affected user group.
This attack incident raises the question: is DeFi's "decentralization" a revolution in technical architecture or a reconstruction of trust models? When the balance between innovation and security is disrupted, perhaps returning to the "minimum trust" underlying logic is the only way to find a sustainable balance between efficiency and risk.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。


