Author: Deep Tide TechFlow
The Trump administration launched an official news app on March 27, claiming to allow users to connect to White House information "without filters."
However, several independent security audits revealed a rather ironic fact within 48 hours: the app's installation package embedded Huawei's tracking components, and Huawei is the Chinese company that the U.S. government itself sanctioned for national security reasons.
Additionally, the app requests a series of system permissions far exceeding those needed for news applications, such as GPS location, fingerprint recognition, startup auto-start, and more, prompting X platform to quickly label its official promotional post with a community note warning.
Why does an app that publishes news releases and presidential live streams need to read your fingerprint?
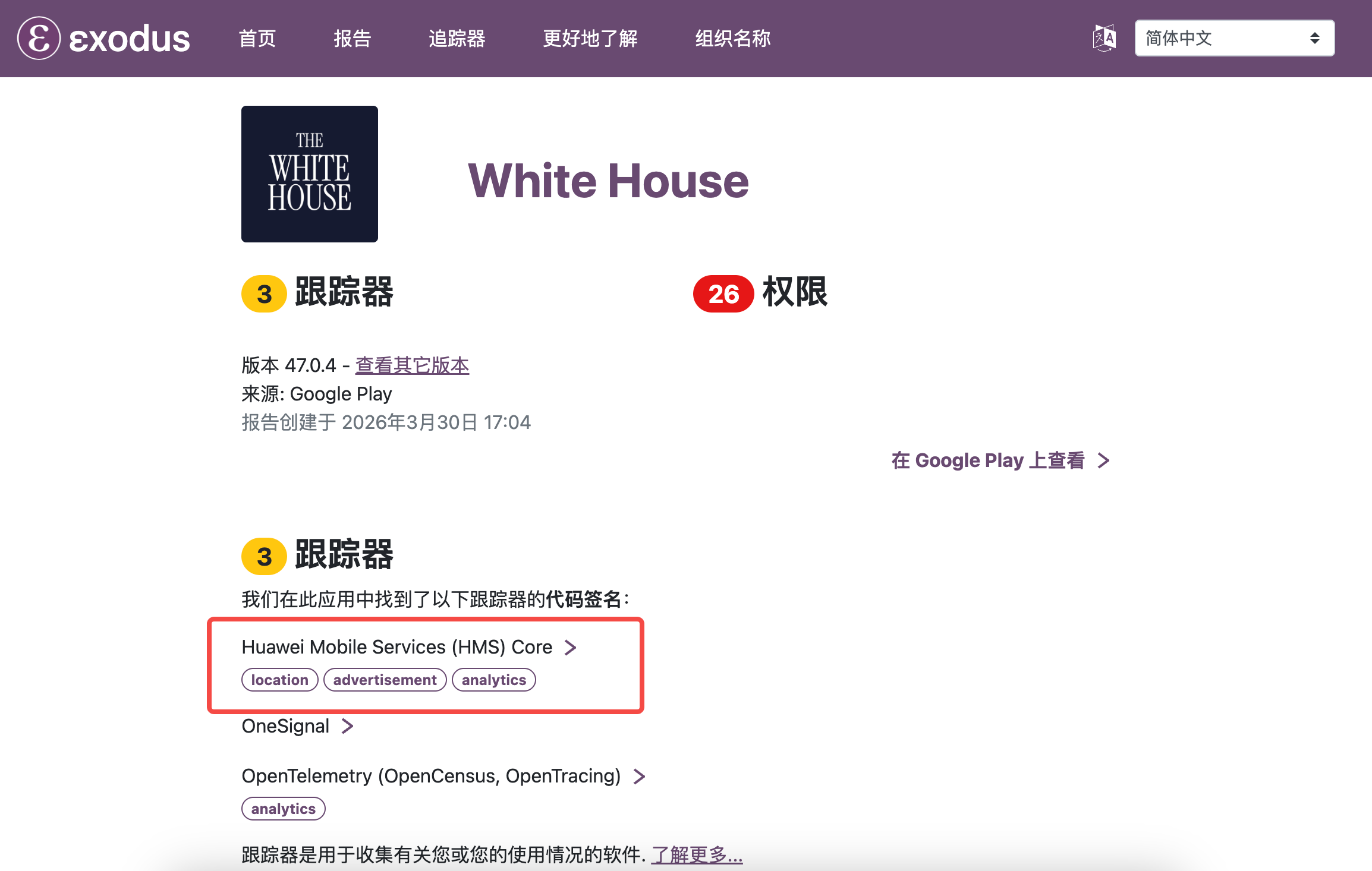
Security researcher Sam Bent conducted a reverse analysis of the White House app (version number 47.0.1) and scanned it via Exodus Privacy. Exodus Privacy is an open-source privacy auditing platform for Android apps, specifically designed to detect embedded trackers and permission requests, widely used in the privacy research community. The scan results showed that the White House app embedded three trackers, one of which is Huawei Mobile Services Core.
IBTimes subsequently reported the same finding, and legal analyst mitchthelawyer also confirmed the conclusion of the Exodus report in a Substack post. Three independent sources pointed to the same fact: the official White House app indeed contains Huawei SDK code.
It should be noted that Huawei Mobile Services Core itself is the push and analytics SDK that Huawei provides for the global Android ecosystem, and many apps targeting the international market embed it for compatibility with Huawei phones.
Its presence in the installation package does not mean it is actively sending data back to Huawei. But the problem is:
The U.S. government bans domestic companies from doing business with Huawei for national security reasons, yet the official presidential app contains Huawei's code. Comments on Hacker News hit the nail on the head: this is likely a default configuration from a contractor, and the decision-makers at the White House may not even be aware of the existence of the Huawei SDK, "but that may be more concerning than intentional embedding."
The list of permissions is comparable to system tools, yet the privacy policy hasn't been updated in a year
The permissions requested by the White House app include: precise GPS location, fingerprint biometric recognition, storage read and write, startup auto-start, overlaying other applications with floating windows, Wi-Fi network scanning, and reading notification badges. In comparison, AP News, which provides similar news push and disaster reporting, requires far fewer permissions than this.
IBTimes pointed out that the app's developer admitted that the technology plugin originally intended to strip location permissions "clearly did not strip any relevant code."
The bigger issue lies in the privacy policy. According to cross-confirmation from IBTimes and mitchthelawyer's Substack article, the privacy policy applicable to the White House app was last updated on January 20, 2025, a full year before the app went live. This policy only covers website visits, email subscriptions, and social media pages, without mentioning mobile apps, GPS tracking, location data collection, or biometric access at all. When users click "agree," they are consenting to a document that does not encompass the app's actual behavior.
Embedded promotional language and immigration reporting access
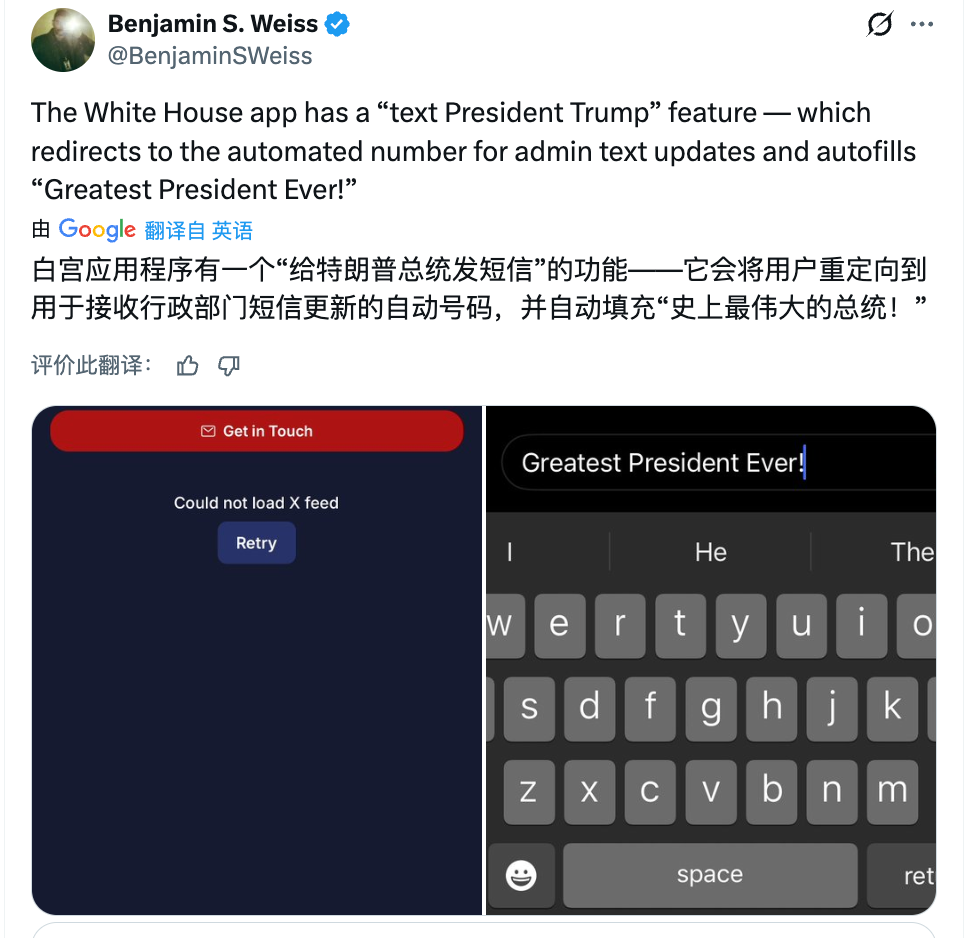
The app contains a "Text the President" feature button. When clicked, the message text box automatically fills in the phrase, "Greatest President Ever!" Users who choose to send it will have their name and phone number collected by the system.
Additionally, the app also embeds an ICE reporting button. ICE is the U.S. Immigration and Customs Enforcement, responsible for immigration enforcement and deportation actions. Clicking this button will directly redirect to ICE's informant reporting page, where users can anonymously report individuals suspected of being illegal immigrants.
A government news release tool in name actually serves as a data collection entry for political propaganda and law enforcement reporting. Within less than two days of its launch, X platform users labeled the White House's official promotional post with a community note, alerting other users to privacy risks.
Not just the White House: FBI app runs ads, FEMA requires 28 permissions
In the same investigation, Sam Bent conducted Exodus audits on multiple federal agency apps and found that the White House app is far from an isolated case.
The FBI's official app "myFBI Dashboard" requests 12 permissions, embedding 4 trackers, including Google AdMob, an advertising SDK. An official app of a federal law enforcement agency reads user phone identity information while serving targeted ads.
The FEMA (Federal Emergency Management Agency) app requests 28 permissions, with its core functions being merely to display weather alerts and shelter locations.
The Customs and Border Protection (CBP) passport control app requests 14 permissions, 7 of which are classified as "dangerous permissions," including background location tracking (tracking continues even after the app is closed) and full storage read/write. The entire CBP application ecosystem retains facial data for up to 75 years, shared among the Department of Homeland Security, ICE, and the FBI.
At a deeper level of data procurement, the Department of Homeland Security, FBI, Department of Defense, and Drug Enforcement Administration purchase over 15 billion location data points daily through commercial data brokers like Venntel, covering more than 250 million devices without the need for a warrant. This operation essentially circumvents the mobile location data privacy protections established by the U.S. Supreme Court in the 2018 Carpenter v. United States case.
Several commenters on Hacker News summarized the common logic of these apps: the government repackages public content that could be released via web pages or RSS into native apps, with the only reasonable explanation being the acquisition of system-level permissions that browsers do not offer, including background location, biometric, device identity reading, and startup auto-start.
The U.S. Government Accountability Office (GAO) report in 2023 shows that out of 236 privacy and security recommendations issued since 2010, nearly 60% have not yet been implemented. Congress has been advised twice to pass comprehensive internet privacy legislation, but no action has been taken so far.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。


