Written by: Eli Nagar
Translated by: Block unicorn
I wrote this article to better understand the topic. Ultimately, it turned into a comprehensive technical report detailing how quantum computers could break Bitcoin, the solutions currently proposed, and how a new "no upgrade required" solution called QSB works.
If you are already familiar with certain parts, feel free to skip ahead.
Part One: The Cryptographic Foundation of Bitcoin
Before diving into quantum threats, I realized it was essential to first understand the underlying mechanics of Bitcoin. Bitcoin relies on various mathematical tools to secure your Bitcoin balance (satoshis). Let's break them down one by one.
Public Key, Private Key, and Address
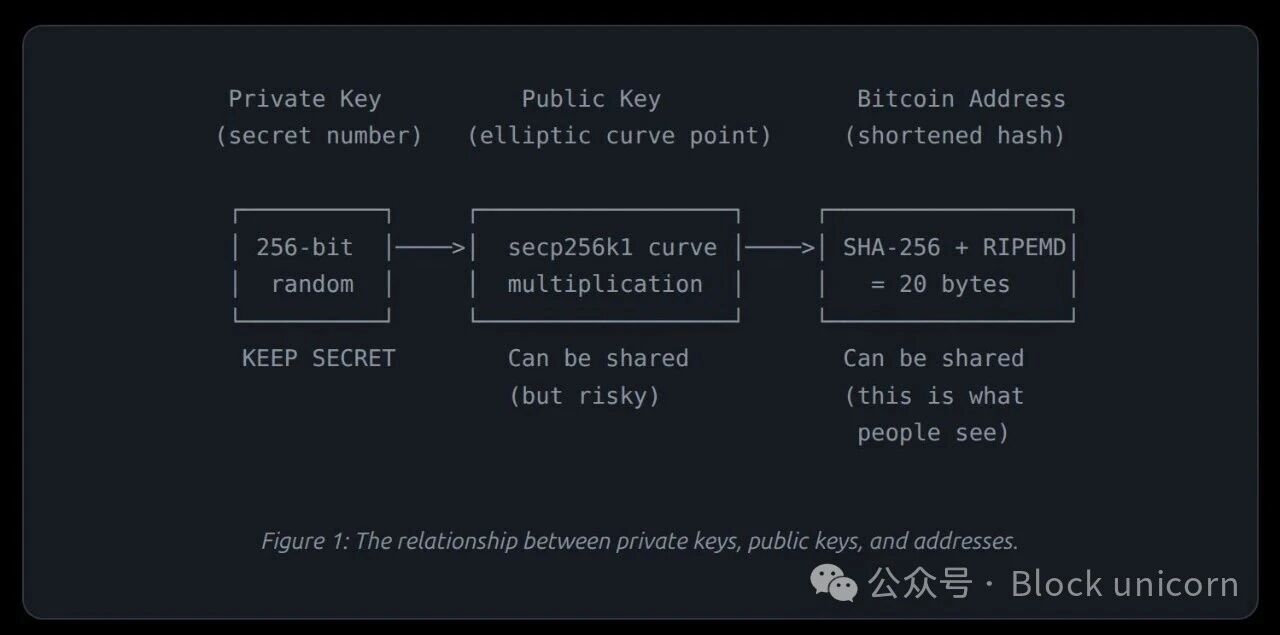
Private Key— a secret, randomly generated number. You can think of it as the password to your Bitcoin wallet. It is a 256-bit number, which means it is selected from approximately 10⁷⁷ possible combinations (more than the number of atoms in the observable universe). If someone knows your private key, they can steal your Bitcoin.
Public Key— a number derived mathematically from the private key using a one-way function called elliptic curve multiplication (remember this). You can share your public key freely; at least under today's computing technology, no one can reverse-engineer the private key from the public key. Bitcoin uses a specific elliptic curve called secp256k1.
Bitcoin Address— a shortened hashed version of the public key. When someone sends you Bitcoin, they send it to your address. The key point is that the address hides the actual public key through two layers of hash algorithms (SHA-256 + RIPEMD-160), adding an extra layer of protection.
How Transactions Are Signed
When you send Bitcoin, you create a transaction and must prove that you own the Bitcoin. You achieve this by generating a digital signature using the ECDSA algorithm (Elliptic Curve Digital Signature Algorithm).
ECDSA (Elliptic Curve Digital Signature Algorithm)— a mathematical program that generates a signature using your private key and transaction data. Anyone can use your public key to verify this signature, but it cannot be forged without the private key. Bitcoin uses ECDSA and the specific curve known as secp256k1.
Digital Signature— a pair of numbers (called r and s) that mathematically prove: "The holder of the private key corresponding to this public key authorizes this particular transaction." Any change to the transaction (even a single byte) will invalidate the signature.
How Mining Uses SHA-256
SHA-256 (Secure Hash Algorithm, 256 bits)
A hashing function. A mathematical "meat grinder." You can input any data (a word, a file, a book), and it will generate a fixed-size 256-bit "fingerprint." The same input always produces the same output, but even a slight change in input will generate a completely different output. The key point is that you cannot reverse-engineer the input.
Bitcoin miners repeatedly hash the block data using the SHA-256 algorithm, trying trillions of different hash combinations every second to find a hash value that starts with a specific number of zeros. This is the "proof of work" that secures the network. The more zeros required, the harder it becomes.
Part Two: Quantum Threats
Things start to get interesting from here. Traditional computers store information in the form of bits. Each bit is either a 0 or a 1. Quantum computers use quantum bits, which can exist in a "superposition" of 0 and 1 simultaneously. This property, along with quantum entanglement (the way quantum bits are interconnected in ways traditional bits cannot be), allows quantum computers to solve certain specific problems at an exponential speed, far exceeding any traditional computer.
When you measure a quantum bit, the superposition collapses, ultimately resulting in either 0 or 1. But before measurement, quantum algorithms can manipulate all possible states simultaneously.
I encountered a recurring question during my research: quantum computers are not "faster computers" in the conventional sense. They are specialized tools that utilize quantum physics to solve specific types of mathematical problems. Unfortunately, two of these problems are directly related to Bitcoin.
Shor's Algorithm: The Key Cracker
Shor's Algorithm
This quantum algorithm was discovered by mathematician Peter Shor in 1994, and it can efficiently solve the discrete logarithm problem and integer factorization problem. These two mathematical problems form the basis of most modern cryptographic techniques, including Bitcoin's ECDSA signature. On a traditional computer, solving these problems would take billions of years. However, on a sufficiently powerful quantum computer, it can be done in just a few hours.
The Key Threat
Shor's algorithm can derive the private key from the public key. If an attacker knows your public key and has access to a sufficiently powerful quantum computer, they can compute your private key and steal your Bitcoin. This completely undermines the ECDSA algorithm.
For Bitcoin’s secp256k1 curve (256 bits), under ideal and error-free conditions, Shor’s algorithm requires around 515 logical quantum bits. However, practical quantum computers have errors. Each "logical quantum bit" (a perfect, error-free quantum bit) requires over 1,000 to 10,000 physical quantum bits for error correction. This results in the actual required number of physical quantum bits being:
The hardware required to crack Bitcoin's ECDSA—early estimates ranged from 4 million to 20 million physical quantum bits (a 2022 study from the University of Sussex estimated that if the attack lasted 1 hour, it would require 317 million physical quantum bits). However, a paper published by Google Quantum AI in March 2026 dramatically reduced this figure to less than 500,000 physical quantum bits, approximately 20 times smaller than previous estimates. This paper proposed two circuit variants: one using ≤1200 logical quantum bits and 90 million Toffoli gates, and another using ≤1450 logical quantum bits and 70 million Toffoli gates. This will be detailed in Part 5.
Grover's Algorithm: The Search Accelerator
Grover's algorithm, discovered by Lov Grover in 1996, can search unordered data at a quadratic speed. If a classical computer needs to check N possibilities, Grover's algorithm only needs √N. For SHA-256 (2²⁵⁶ possible outputs), this means the effective security level decreases from 256 bits to 128 bits.
Wait... this sounds quite frightening, but by modern standards, a 128-bit security level is still considered unbreakable. Additionally, Grover's algorithm has a critical limitation: it does not excel at parallelization. Running k quantum computers only yields a k^(1/2) speedup, rather than scaling linearly by k^(x) as classical computers do. This makes classical mining hardware (ASIC) still more practical for the foreseeable future.
Attack Window
When you spend Bitcoin, your transaction is broadcast to the network and stays in the memory pool (a waiting area) for about 10-60 minutes before being confirmed and packaged into a block. During this time, your public key is exposed in the transaction data.
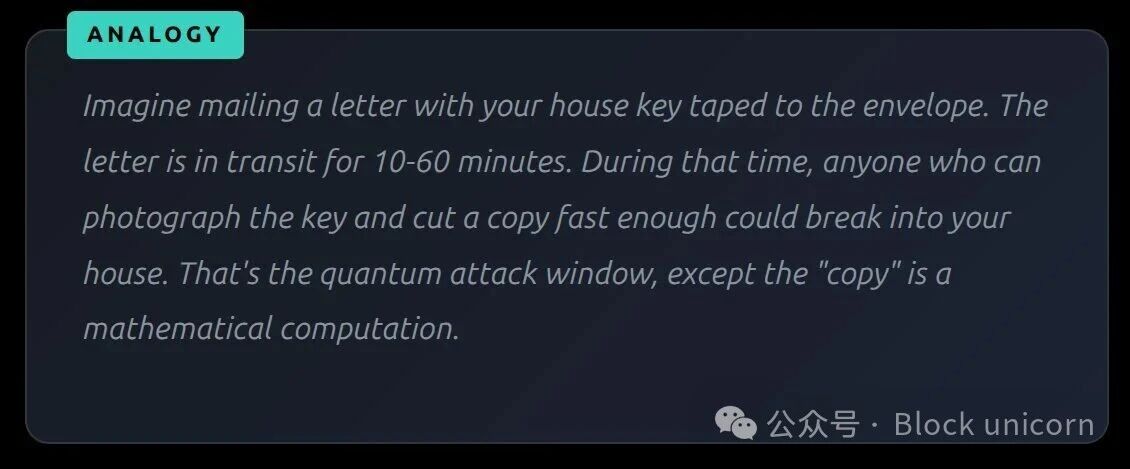
A quantum attacker observing the memory pool can see your public key, derive your private key, construct a competing transaction to send your Bitcoin to themselves, and potentially confirm it before your legitimate transaction (if they also have mining resources). The entire attack process must be completed within a few minutes.
However, for certain types of old Bitcoin (which will be detailed in the next part), the public key has been permanently recorded on the blockchain. In this case, there is no time window. An attacker could spend an arbitrary amount of time.
Part Three: The Risks Involved
Exposed Public Keys vs. Unexposed Public Keys
This is where I began to realize that the situation is far more complex than "quantum attack = all Bitcoin is doomed." Not all Bitcoin is equally vulnerable. The critical question is: Is the public key visible on the blockchain?
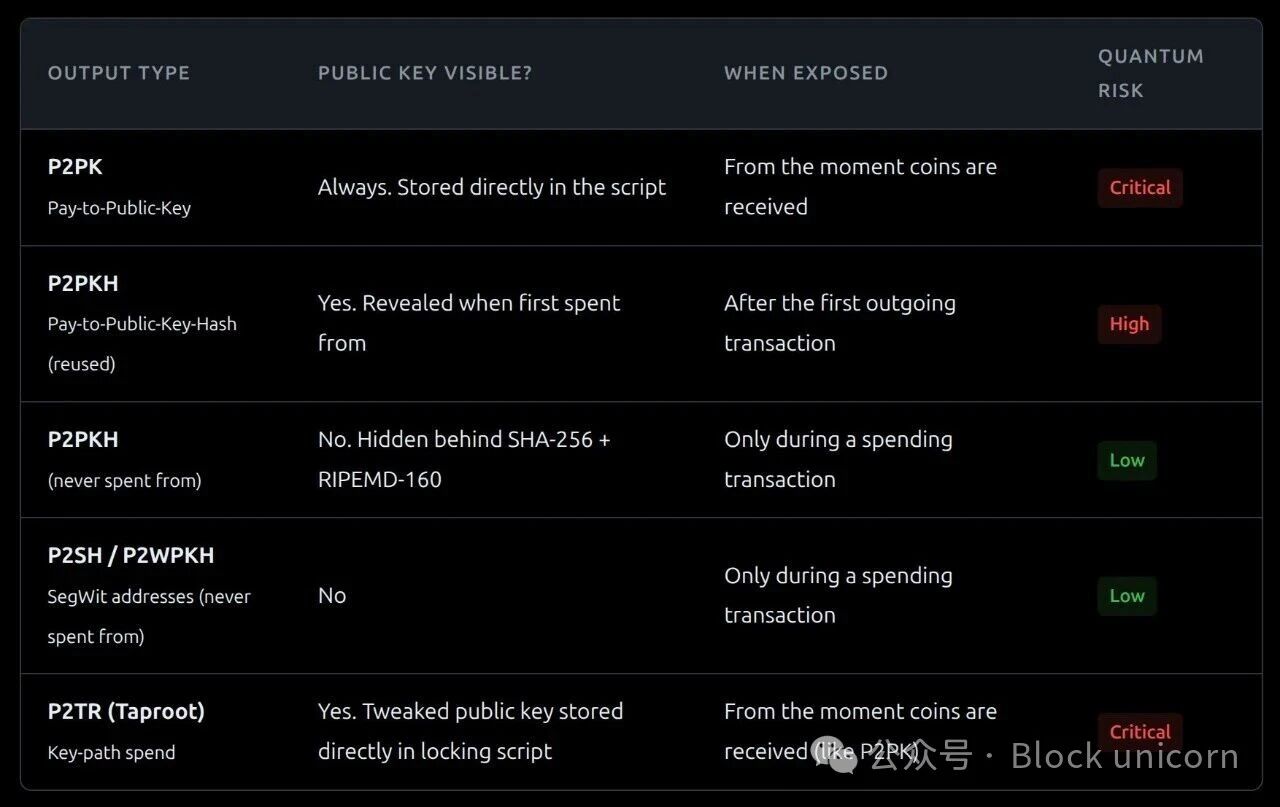
P2PK (Pay-to-Public-Key)
The earliest Bitcoin output format, used from around 2009 to 2012. The complete public key is written directly into the transaction. Early Bitcoin miners, including Satoshi Nakamoto, used this format. This type is the most vulnerable.
P2PKH (Pay-to-Public-Key-Hash)
The standard format that replaced P2PK. It does not store the public key directly but instead stores the hash value (fingerprint) of the public key. The actual public key is revealed only when you make a spend from that address. This provides a layer of quantum protection, assuming you never reuse that address.
Address Reuse
Sending Bitcoin multiple times from the same address. The first time you spend from a P2PKH address, your public key is leaked in the transaction. If there is still remaining Bitcoin in that address, that Bitcoin is now exposed as the public key is permanently recorded on the blockchain.
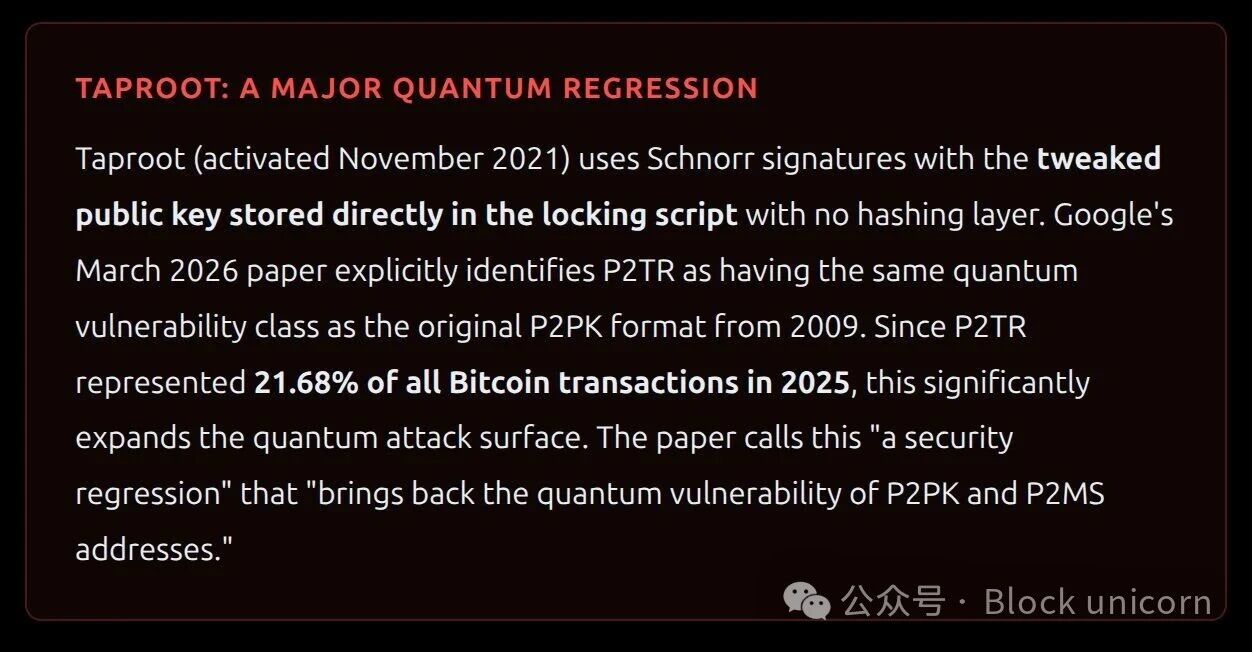
P2TR (Pay-to-Taproot)
The latest standard output format for Bitcoin, introduced in November 2021 with the Taproot upgrade. P2TR uses Schnorr signatures (a more efficient alternative to ECDSA) and supports two consumption paths: a simple "key path" consumption and a more complex "script path" consumption, the latter supporting advanced smart contract features. From the perspective of quantum mechanics, the issue is that P2TR directly stores the modified public key in the locking script, without a hashing layer to conceal it. This means that from the moment Bitcoin is received, the public key is as visible on the blockchain as in the old P2PK format from 2009. The address starts with bc1p.
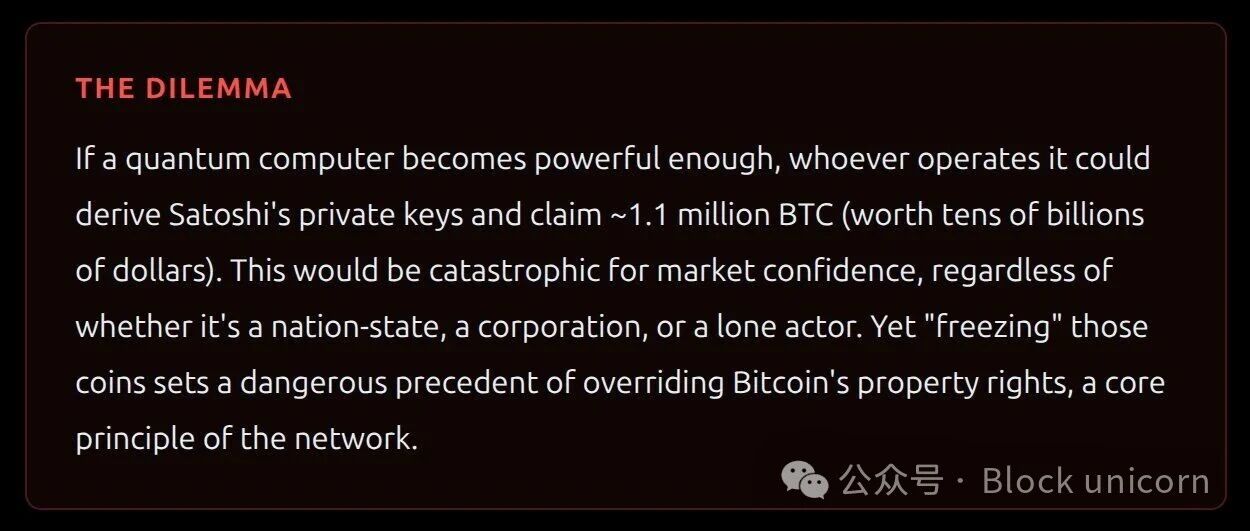
The Satoshi Problem
This section truly sparked my thoughts. The anonymous creator of Bitcoin, Satoshi Nakamoto, mined around 1.1 million Bitcoins in the early days of the network (2009 - 2010). These Bitcoins exist in P2PK form. Since the day they were mined, their public key has been openly maintained on the blockchain.
These Bitcoins have never been transferred. Most people believe the private key was either intentionally abandoned or lost. This creates an unsolvable problem: no post-quantum migration scheme can securely transfer these Bitcoins, as migration requires the private key.
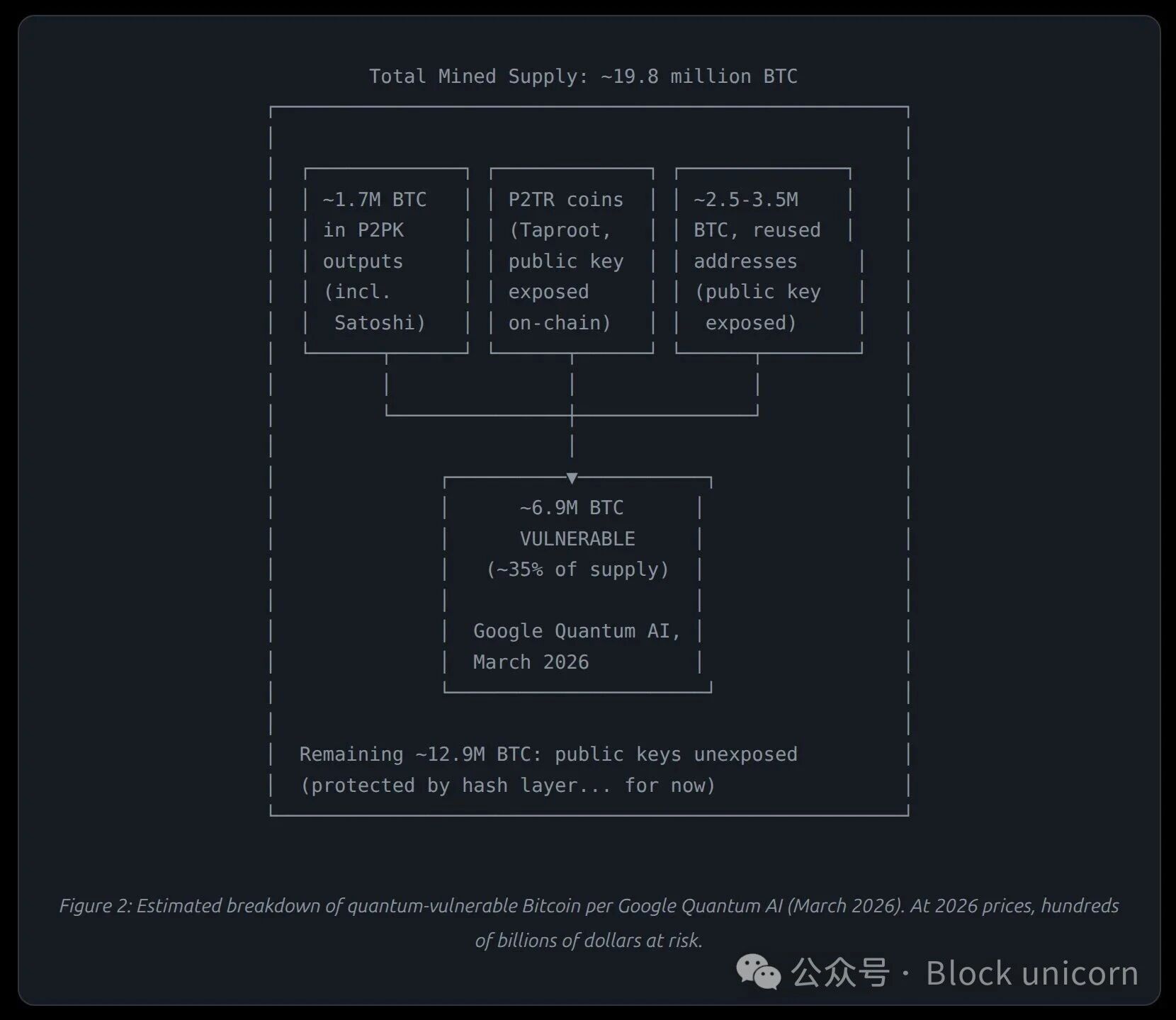
How Many Bitcoins Are at Risk
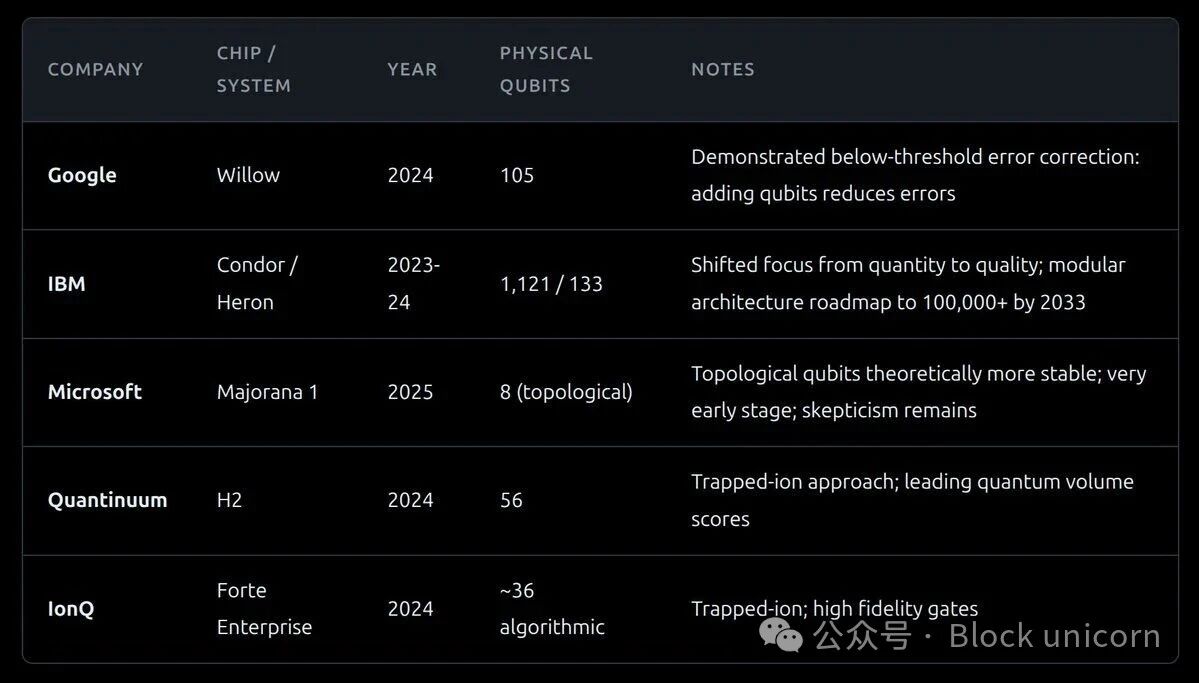
Part Four: The Current State of Quantum Hardware
So how worried should we actually be? To answer this question, I researched the current state of quantum computing hardware and what it needs to achieve to pose a threat to Bitcoin.
The Gap: Smaller Than We Think
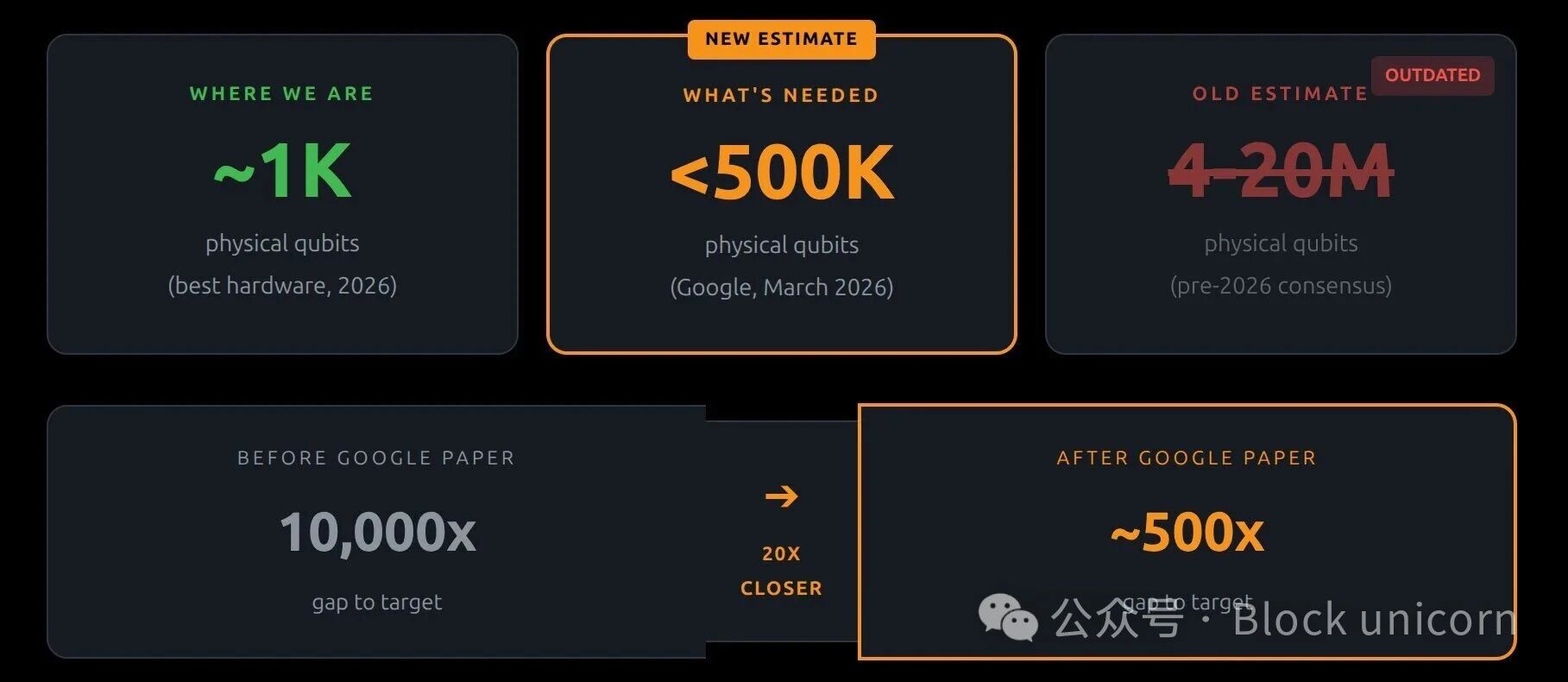
Revised Timeline (After Google Paper Publication)
Before the publication of the Google paper, most experts believed that the emergence of cryptographically relevant quantum computers (CRQC) would occur between 2035 and 2050. The reduction of resources by a factor of 20 has significantly shortened this timeline. Google itself has set a deadline of 2029 to migrate its authentication services to post-quantum cryptography. PC Gamer reported that Google estimates a 10% probability of achieving "Quantum Day" by 2032. The paper noted that "advancements in quantum algorithms and error correction architectures continue to significantly reduce the physical resources required," and that "algorithms are always being improved." IBM’s 2029 roadmap aims for about 200 logical quantum bits, although still below the required 1200, the gap is shrinking non-linearly.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




