Solana will launch post-quantum migration, primarily promoting the Falcon algorithm to ensure wallet and consensus security and clearly outline implementation steps.
Written by: David Rubin, Emanuele Cesena, Maher Latif
Translated by: Saoirse, Foresight News
Quantum computers do not currently pose a direct threat to Solana, but the public chain must prepare in advance, gradually transitioning to a post-quantum encryption system. This article will detail the migration plan for transaction signatures, consensus mechanisms, and existing wallets while keeping up with the latest technology iteration trends to retain ample flexibility for future adjustments.
Public key encryption is the underlying foundation of all operational logic in blockchain. Users authorize each transaction through signatures, and validation nodes package blocks and sign certificates to finalize the consensus across the network. Whether it is asset ownership or on-chain consensus mechanisms, the core logic relies on public key verification of signature validity.
In the decentralized, permissionless public chain ecosystem, a legitimate signature is the only proof of authorization. As long as a valid signature can be generated from the account's public key, the corresponding account's assets can be controlled. This system has operated stably for a long time, with the key being the one-way irreversibility of keys: a private key can easily be derived from a public key, but it is nearly impossible to reverse-engineer a private key solely from its public key.
However, quantum computing is breaking this security barrier. Once high-performance quantum computers are fully developed, all currently used signature algorithms based on elliptic curves will be compromised, posing a complete threat to user asset security and the consensus stability of the entire public chain.
Therefore, for Solana to build a robust post-quantum security system, it must specifically address three core risk points: consensus mechanisms, transaction signatures, and existing wallet migration. The technical limitations and performance standards of these three modules vary, requiring separate planning and phased implementation.
This article will comprehensively introduce Solana's overall quantum migration plan. The Falcon algorithm has become the preferred choice due to its smaller signature size and stronger adaptability. Meanwhile, various core components can independently complete upgrades based on their own bandwidth limitations and development needs.
Latest Developments in Quantum and Post-Quantum Technologies
The latest industry research released by Google, NVIDIA's continued increase in investment in quantum research, and the rapid development of quantum error correction technology and supporting tools all signify that the blockchain industry urgently needs to formulate a quantum defense roadmap and initiate public community discussions.
We clearly judge that quantum computers will not threaten Solana's network security in the short term. The industry generally estimates that quantum attack techniques capable of breaking elliptic curve encryption will require several more years to materialize. Meanwhile, Solana continues to maintain high-frequency version iterations and ecosystem updates.
Given that post-quantum encryption technology is still under continuous research and optimization, the team will track various alternative solutions in the long run, ensuring that all future protocol upgrades adopt the most mature and reliable technologies available, avoiding hasty decisions.
To date, only ML-DSA (Dilithium, a mainstream post-quantum signature algorithm) has received formal standardization certification from the U.S. National Institute of Standards and Technology (NIST), and FN-DSA (Falcon, a lightweight post-quantum signature scheme) will also complete the entire standardization process within a few months.
Long-term upgrade planning provides us sufficient time to filter encryption schemes that better align with Solana's high-performance attributes. Global research teams continue to develop a new generation of quantum-resistant encryption technologies, which are expected to yield high-quality algorithms more suitable for the Solana ecosystem in the future.
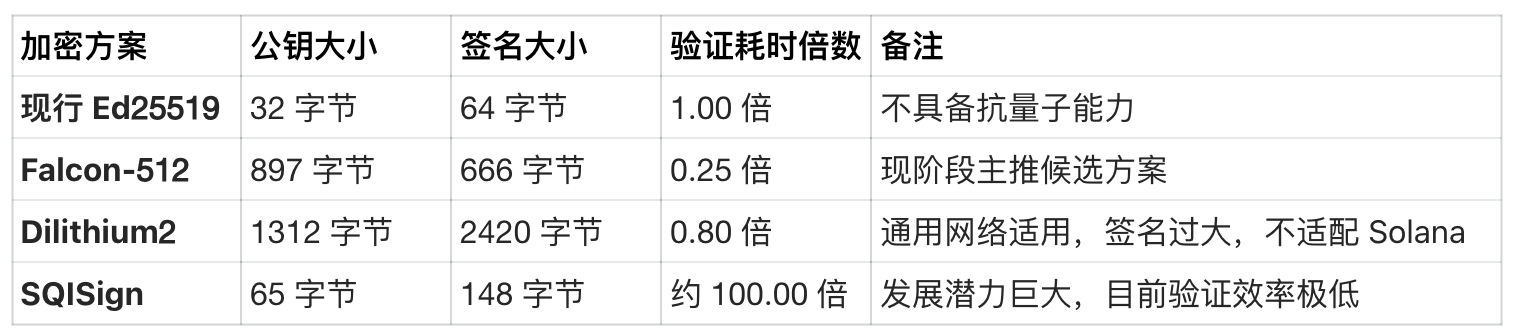
SQISign is a promising alternative technology: its public key and signature sizes are much smaller than mainstream solutions like Falcon and ML-DSA, but its shortcoming lies in extremely slow signature verification speeds, making it currently unsuitable for large-scale commercial use. If breakthroughs in algorithm efficiency are achieved later, it could become a highly competitive alternative solution.
Currently, most post-quantum signature algorithms have significant drawbacks: the volume of public key and signature data is too large. This greatly increases the data size of a single transaction and node consensus voting, which would seriously hinder network operation efficiency for Solana, which seeks ultra-high throughput.
Consensus Mechanism
Solana's current Alpenglow consensus protocol employs the BLS12-381 signature algorithm, with the core advantage being support for efficient signature aggregation. In this mechanism, the votes of validating nodes are all BLS signatures, and the final block compliance certificate is generated by aggregating the signed votes from all network nodes.
An ideal post-quantum consensus layer must retain the core capability of signature aggregation. The Falcon aggregate signature technology implemented based on the LaBRADOR proof system has already verified the feasibility of this model.
Regarding the consensus scenario where all validating nodes sign the same information, the grouped multi-signature protocols (e.g., Raccoon, DOTT) are currently in key research and development stages, making them a viable direction for the consensus layer upgrade.
The signature algorithm used in the consensus layer can operate independently of the transaction signature algorithm. Just as the current Alpenglow consensus uses BLS12-381 while transactions uniformly adopt Ed25519, in the post-quantum upgrade, the consensus layer can opt for a dedicated cryptographic solution that better fits aggregation needs and low-latency characteristics.
Transaction Signature
Among several post-quantum signature standards certified by NIST, Falcon has the smallest signature size, which is crucial for Solana, which heavily relies on bandwidth efficiency.
Previously, due to high development implementation difficulty and vulnerability to side-channel attacks, Falcon's standardization process was delayed; however, its core advantages remain irreplaceable:
- Falcon signature verification uses only integer operations, making the logic straightforward and implementation easy;
- The entire signature operation is completed off-chain, allowing wallet operators and nodes to choose a version of the program that has undergone strict security audits.
As mentioned above, SQISign is another highly promising alternative solution, with its public key and signature sizes extremely compact, approaching traditional elliptic curve algorithm levels. Although the security and operational performance of this technology continue to optimize, it has not yet completed standardization and still belongs to the cutting-edge research phase.
Existing Wallets
The smooth transition of existing wallets and asset migration is a critical issue that cannot be overlooked. For established public chains like Bitcoin, figuring out how to protect assets in old wallets and ensuring a secure migration to a quantum-resistant encryption system has always been a challenge in the industry.
Fortunately, Solana has a complete and feasible full wallet migration plan. In Solana's current Ed25519 encryption system, private keys are generated from a 32-byte raw seed. During the signing process, the system computes the secret key using the SHA-512 algorithm, from which the public key and transaction signature are derived.
Even if future quantum computers break the Ed25519 encryption mechanism, attackers can at most only steal the derived secret keys and cannot decrypt the user's original seed. SHA-512 remains a secure and reliable quantum-resistant one-way hash algorithm, capable of permanently safeguarding user seed security.
Quantum attackers cannot access the core original seed, so the unique control of assets remains in the hands of legitimate holders. Based on this characteristic, we planned a complete migration process:
- All new wallets will fully adopt post-quantum secure signature solutions like Falcon;
- Gradually phase out and shut down Ed25519 signature verification to prevent quantum devices from forging signatures and stealing user assets;
- Existing users migrating assets must present a valid signature from the new post-quantum key pair and submit zero-knowledge proofs to demonstrate ownership of the original Ed25519 seed.
This migration mechanism completely separates from the old signature system that poses security risks, ensuring that only genuine asset holders can produce compliant zero-knowledge proofs, thereby comprehensively securing asset migration. Several mature zero-knowledge proof frameworks can adapt to this mechanism; although the general proof documents may be large, asset migration is only a one-time operation that will not affect regular on-chain transaction experiences.
Program Derived Accounts (PDA) are a unique type of account exclusive to Solana, inherently designed without private keys, thus possessing inherent quantum safety properties that require no modifications or upgrades.
Other Supplementary Notes
Several core supporting modules of the Solana network also rely on Ed25519 signatures, including the block sharding transmission protocol Turbine, node peer-to-peer communication Gossip, and QUIC fast transmission protocol. The encryption upgrade plans for these components will align with the transformation of transaction signatures.
Currently, Solana's operational environment has opened various elliptic curve encryption interfaces to developers, covering Ed25519, Secp256k1, Secp256r1, BLS12-381, etc. Once entering the post-quantum era, these traditional encryption interfaces that have security vulnerabilities will all be shut down and replaced with new-generation secure encryption underlying tools.
The community is also voluntarily conducting experimental technology research and development. For example, the Blueshift team has utilized existing on-chain native components combined with the Winternitz one-time signature (WOTS) technology to implement a quantum-resistant cold wallet storage solution without requiring protocol-level upgrades, providing users with additional security protections of their choice.
Solana's Future Development Plans
The public chain's immediate focus is to implement the SIMD-0416 proposal, adding Falcon signature verification system call interfaces for smart contracts. After achieving on-chain native Falcon verification, developers can independently integrate this cryptographic algorithm to build quantum-resistant asset vaults, secure transfer protocols, and various DeFi basic infrastructures.
This does not mean Solana will directly designate Falcon as the unified protocol-level signature scheme for the entire network, nor will it forcibly integrate it into the Alpenglow consensus system. Solana will continue to maintain a rapid iterative development pace, while post-quantum cryptography is still in a phase of continuous exploration and improvement. The core strategy of the team is to prioritize the implementation of short-term feasible secure solutions while longitudinally evaluating various cryptographic technologies for future protocol iterations to筛选 the most optimal long-term solutions.
At the client development level of Firedancer, we have completed a highly optimized Falcon signature verification program, achieving operational efficiency 2-3 times that of the official reference version, and will subsequently advance comprehensive performance testing and security audits. Meanwhile, the team will continue to evaluate various alternative cryptographic schemes to build a sufficient technical reserve for Solana's long-term quantum security strategy.
References
[1] R. Babbush, H. Neven. "Safeguarding cryptocurrency by disclosing quantum vulnerabilities responsibly." Google Research Blog, March 2026.
https://research.google/blog/safeguarding-cryptocurrency-by-disclosing-quantum-vulnerabilities-responsibly/
[2] NVIDIA. "NVIDIA Launches Ising, the World’s First Open AI Models to Accelerate the Path to Useful Quantum Computers." NVIDIA Newsroom, March 2026.
https://nvidianews.nvidia.com/news/nvidia-launches-ising-the-worlds-first-open-ai-models-to-accelerate-the-path-to-useful-quantum-computers
[3] A. Sanso. "So you wanna Post-Quantum Ethereum transaction signature." Ethereum Research, December 2024.
https://ethresear.ch/t/so-you-wanna-post-quantum-ethereum-transaction-signature/21291
[4] A. Sanso. "Falcon as an Ethereum Transaction Signature: The Good, the Bad, and the Gnarly." Ethereum Research, January 2025.
https://ethresear.ch/t/falcon-as-an-ethereum-transaction-signature-the-good-the-bad-and-the-gnarly/21512
[5] A. Sanso. "The road to Post-Quantum Ethereum transaction is paved with Account Abstraction (AA)." Ethereum Research, February 2025.
https://ethresear.ch/t/the-road-to-post-quantum-ethereum-transaction-is-paved-with-account-abstraction-aa/21783
[6] A. Sanso, T. Thiery, B. Wagner. "Revisiting Falcon signature aggregation for PQ mempools." Ethereum Research, March 2026.
https://ethresear.ch/t/revisiting-falcon-signature-aggregation-for-pq-mempools/24431
[7] D. J. Bernstein et al. "Ed25519: High-speed high-security signatures." 2012.
https://ed25519.cr.yp.to/
[8] NIST. "Post-Quantum Cryptography Standardization." FIPS 203, 204, 205. August 2024.
https://csrc.nist.gov/projects/post-quantum-cryptography
[9] V. Buterin. "How to hard-fork to save most users' funds in a quantum emergency." Ethereum Research, March 2024.
https://ethresear.ch/t/how-to-hard-fork-to-save-most-users-funds-in-a-quantum-emergency/18901
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




