Do not only look at audits and TVL, these are the real risks.
Written by: Liam Akiba Wright
Translated by: Luffy, Foresight News
In 2026, before users deposit into DeFi, they will face a problem that audits and total locked value (TVL) cannot solve: which links will collapse under extreme market conditions.
This is also the core transformation of all rigorous risk control assessments this year. The security report for the first quarter of 2026 shows that the industry has experienced 44 security incidents, with stolen funds totaling 482 million dollars, among which six audited protocols were still attacked by hackers.
An analysis of a cryptocurrency theft related to North Korea on April 30 noted: as of April this year, only two major theft incidents accounted for 76% of the total hacker theft across the network. The root causes of incidents are no longer just code vulnerabilities, but also include multiple issues such as the disclosure of signer private keys, governance authority loopholes, cross-chain bridge validation defects, missing time lock mechanisms, and insufficient emergency response capabilities.
For ordinary users, this lesson is very straightforward. DeFi platforms are complex systems composed of layers of components including smart contracts, administrator private keys, governance mechanisms, token incentives, stablecoins, cross-chain bridges, oracles, front-end interfaces, risk control rules, and emergency privileges.
Choosing whom to trust fundamentally means assessing whether these underlying links are transparent, whether they have been tested in practice, whether risk control is conservative, and whether they can match the risk level of your invested funds.
No checklist can guarantee the absolute safety of DeFi platforms. What we can do is filter out the highest-risk inferior projects first, and not be misled by yield, brand endorsements, or trends on social media.
Traditional screening indicators have fatal blind spots
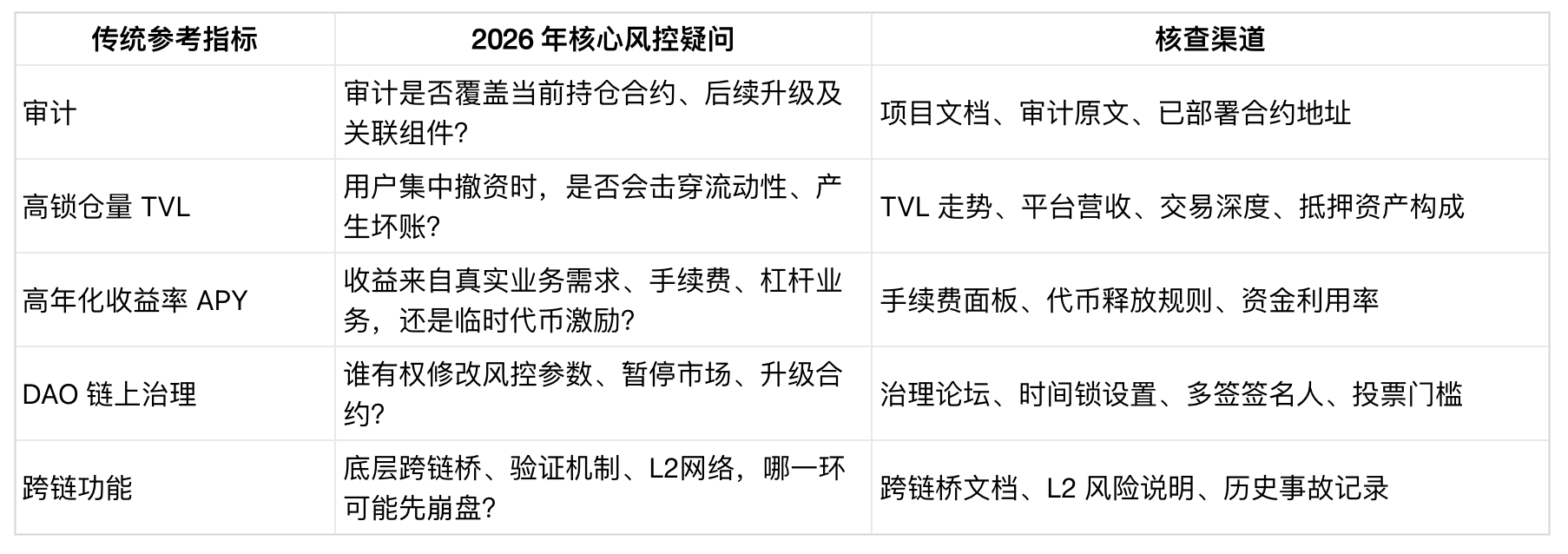
In the past, the lazy screening logic of users was simple: check if there is an audit, look at the locked amount TVL, compare annualized returns, and see if whales are using it. However, these indicators have limitations and cannot fully assess safety.
Code audits are only meaningful when they cover the current actual managed fund contracts. Many protocols upgrade contracts after completing audits, relying on unaudited adaptation layers, cross-chain bridge contracts, oracle setups, or backdoors in administrator permissions, making old audit reports directly invalid. Truly reliable audits must disclose audit scope, vulnerability details, and links to deployed contracts; simply displaying an audit badge with no date or scope has very low reference value.
The locked amount only reflects superficial liquidity and cannot reflect the risk resistance capability under extreme market conditions.
Revenue rankings can help distinguish between protocols profiting from real transaction fees and those merely surviving on token mining incentives. Some platforms have a high locked amount but weak revenue, relying on short-term subsidies and fragile collateral asset structures. Once users withdraw en masse, it is easy to encounter runs and bad debts.
The annualized percentage yield (APY) is the least reliable trust indicator. An ultra-high APY often compensates for various hidden risks: risks from contract vulnerabilities, oracle failures, collateral asset collapses, liquidation risks, cross-chain bridge risks, and risks of reward token value crashes. The most critical questions to ask are: where does the yield come from? What links need to be error-free for you to withdraw smoothly?
Before making a deposit, first understand the project's permission control
Professional DeFi risk control starts with figuring out: who and what mechanism has the authority to change system rules.
Key checks should include contract upgrade permissions, time lock mechanisms, governance voting thresholds, multi-signature signer compositions, market suspension permissions, oracle control, liquidation rules, risk control parameter adjustment processes, and emergency response mechanisms. If this information is unclear, it is a huge risk signal; even if the information is public, if permissions are concentrated in a very small number of hands, it similarly hides dangers.
Regulatory policies on DeFi also focus on governance rules, responsible parties, operational risks, conflict handling, information disclosure, and technological risk control. The reason is simple: many protocols superficially claim to be decentralized, only for users to later find that actual control is highly centralized.
The most practical standard for ordinary users is whether the project clearly discloses who has emergency intervention authority and where the boundaries of power lie. Public governance processes, time lock mechanisms, and open debates on risk control parameters are all positive additions.
The worst type of platforms cannot clearly state who controls contract upgrades, how fast rules can change, whether the administrator's private key is under multi-signature custody, who the signers are, or how to respond in an emergency after oracle/cross-chain bridge/market collapses. In such projects, you are not only gambling on code safety but also trusting unknown operators.
Risk control checks should also extend to the underlying architecture: if DeFi relies on L2 networks, cross-chain bridges, or cross-chain collateral assets, any vulnerabilities in the underlying architecture will transmit risks upward.
The multiple security incidents in 2026 have proven that the reasons for collapses have already surpassed traditional smart contract vulnerabilities, with more emerging from key disclosures, governance loopholes, exposure of multi-signature permissions, deficiencies in cross-chain bridge mechanisms, and improper emergency decision-making. Therefore, assessing security requires examining not only the contract itself but also screening all surrounding weak links.
Check historical safety and emergency response capabilities
Before depositing, be sure to search for the historical theft records of the project's public chain, cross-chain bridge, and core collateral assets on security incident tracking platforms. Public hacker incident panels and industry security APIs can serve as preliminary references but should not be taken as final conclusions.
Having been hacked does not mean immediate abandonment; it depends on how post-incident handling is managed; a zero-incident history does not mean there are no potential vulnerabilities. The key is to look at risk patterns: whether incidents are frequent, whether losses have been uncompensated, whether information disclosure is vague, whether incident reviews are superficial, whether contract code plagiarism poses risks, and whether the team’s response attitude during crises shows concern for victim compensation.
The long-tail effect of historical thefts is significant: being hacked once will drag down treasury funds, project reputation, and token value for a long time; the capability for post-incident repair and compensation, in itself, is a credit endorsement.
Quality platforms will proactively disclose their own safety status, including the latest audit reports, vulnerability bounty programs, information disclosure channels, emergency response contacts, and crisis management rules for white hat hackers.
Vulnerability bounty platforms allow users to compare different projects based on bounty amounts, covered assets, total locked value (TVL) in the treasury, update dates, and response data. The Whitehat Safe Harbor framework further enhances security by providing pre-authorized rescue terms for participating protocols.
However, these measures still cannot completely avoid risks. Low bounty amounts, delayed processes, and limited coverage; even with good paper rules, they cannot withstand real market panic tests.
Willingness to invest in bounties, proactively disclose risks, and preset white hat rescue rules at least indicate that the project has seriously considered risk mitigation before incidents occur.
Ordinary users do not need to audit the code line by line but can make a simple judgment: does the platform use plain language to explain the core risk control vulnerabilities and response plans?
The quality of post-incident review reports is also an important indicator. A reliable review will clarify root causes, affected contracts, loss pathways, impact on users, compensation schemes, subsequent risk control rectifications, and unexplored risk boundaries. Vagueness after crises and evasion of key issues are significant red flag signals.
See through the financial logic behind high yields
Even if a platform technically appears sound, if its financial performance is poor, it is still not worth depositing funds.
First, consider the source of income: is it from lending demand, transaction fees, liquidation earnings, real asset yields, staking mining, token issuance subsidies, loyalty programs, leveraged earnings, or a cycle of funds built from borrowing?
Next, simulate extreme scenarios: once incentives diminish, collateral assets plummet, fund utilization rates change, or cross-chain stablecoins detach from their pegs, can the platform stabilize?
Income quality reflects whether users are paying for products without subsidies, liquidity depth reflects whether deposits can be withdrawn without severe slippage, and collateral quality determines whether a low-quality asset collapse can drag down an otherwise legitimate DeFi protocol.
Multiple historical chain liquidation events have confirmed that a single point of failure in cross-chain bridges or validation mechanisms can quickly trigger panic and fund flight, resulting in chain collapses. The most intuitive risk feeling for users is asset freezing, discounted withdrawals, market suspensions, delayed exits, bad debts, and unclear responsibilities.
Stablecoins deserve to be listed separately in the assessment checklist. A forecast report released in 2025 highlighted that the stablecoin market size has reached hundreds of billions of dollars, focusing on reserve asset quality, run risks, concentration, and intermediary roles.
DeFi platforms integrating stablecoins like USDC and USDT bear risks not only from their own contracts but also from issuer policies, reserve management, freezing powers, and the platform's liquidity dependence on a single stablecoin.
Although stablecoins have good liquidity, users must clearly understand which stablecoins the platform relies on, what management powers the issuers hold, whether there are alternative collateral assets, and how the protocol responds to detachment, freezing, and market suspension in extreme cases.
Regulatory transparency should also be given equal importance. The EU MiCA regulation provides users with qualification inquiry channels, but a white paper listing does not represent official endorsement. Registered qualifications, white papers, and reputable operators can only reduce some uncertainties, not serve as absolute safety certifications.
Classify risk signals and then decide on the scale of investment
A simple and practical screening method is to categorize DeFi platform risks into three levels: green light, yellow light, and red light.
Green light safety signals
Complete audits with clear scopes and dates, publicly traceable deployed contracts, reasonable time locks, transparent on-chain governance, conservative collateral asset admissions, clear oracle design, real sustainable revenue, sufficient trading depth, high bounty amounts, comprehensive information disclosure channels, mature emergency plans, and sincere and complete incident review reports.
Yellow light warning signals
Newly launched projects, highly reliant on mining incentives, opaque multi-signature information for administrators, complex cross-chain mechanisms, aggressive acceptance of high-risk collateral assets, limited bounty coverage, weak revenue, and governance rules that are obscure and difficult to understand.
Red light high-risk signals
Anonymity of the team and hidden authority, lack of valid and latest audits, no clear contract upgrade process, no information disclosure channels, no bounties, absurdly high yields, vague logic of cross-chain assets, unresolved historical incidents, inflated TVL data, and intentional promotion of safety while concealing underlying control vulnerabilities.
Then, based on the risk grade, control the investment amount, separating the risks of custody private keys from the risks of the protocol itself; before making large investments, test the withdrawal process with small amounts first.
Avoid investing emergency funds into systems with delayed withdrawals, complex collateral processes, or unclear administrator authorities. After platform upgrades, governance votes, new collateral additions, cross-chain bridge changes, or significant market fluctuations, be sure to reassess the platform.
In 2026, high-quality DeFi platforms will no longer lead users to blind faith but will make risks verifiable: which rules can be modified, who has the authority to modify them, which links may collapse, how the risk warning mechanism works, how researchers are rewarded for safety, whether funds can exit smoothly, and how risks are mitigated after optimistic market scenarios fail.
This is the core standard; if a platform cannot explain all its collapse risks in plain language, users should not put their own funds at risk to test it.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




