Author: Fairy, ChainCatcher
Editor: TB, ChainCatcher
“Hello, this is the Coinbase security team. We have detected unusual login activity on your account…”
The voice on the other end is professional and urgent, even accurately stating your name, registered email, and recent transaction history. Would you choose to hang up immediately, or follow the "customer service" instructions to gradually transfer your funds to a so-called "secure wallet"?
Recently, multiple Coinbase users have been scammed, resulting in staggering losses. In March alone, stolen funds have exceeded $46 million, with annual losses due to social engineering scams for Coinbase users reaching as high as $300 million.
However, how are these hackers able to precisely target their victims? How do they obtain users' personal information? This security crisis may be more severe than imagined.
Scams Rampant, Phishing Attacks Industrialized
On March 28, on-chain detective ZachXBT revealed that in the past two weeks, several cases of suspected scams targeting Coinbase users have occurred, causing the total amount stolen in March to exceed $46 million.
In fact, these types of scams have long been traceable. As early as early February, ZachXBT exposed that between December 2024 and January 2025, Coinbase users lost up to $65 million due to similar tactics, a figure that puts Coinbase at risk of over $300 million in annual social engineering scam losses.
According to ZachXBT's analysis, the scam methods have formed a mature industrial chain:
- Scammers Impersonate Coinbase Officials
Scammers use forged phone numbers to call victims and leverage users' personal information to gain trust. They claim that unauthorized login attempts have been detected on the user's account, enticing victims to cooperate with security verification.
- Sending Phishing Emails
Scammers send forged Coinbase emails containing fake case numbers (Case ID).
- Guiding Users to Transfer Funds
Scammers instruct victims to transfer funds to a fake Coinbase Wallet and whitelist the scam address, claiming this is a method of account security verification.
- Cloning the Coinbase Website
Scammers create nearly 1:1 copies of the Coinbase phishing website and send different operational prompts to victims through forged emails and Telegram scam panels.
In addition, according to Cointelegraph, several cryptocurrency users have recently received scam emails impersonating Coinbase and Gemini. These emails typically claim that due to regulatory requirements, users must transition to self-custody wallets, setting April 1 as the deadline to create a sense of urgency.
The emails provide links to download Coinbase Wallet or Gemini Wallet, along with pre-generated recovery phrases. Once users create new wallets using these phrases and transfer assets, the funds can be instantly drained by the scammers.
Internal Data Access Issues Come to Light
The core of social engineering scams lies in precise information acquisition, and in the cases of Coinbase users being scammed, attackers seem to have obtained victims' personal information, including phone numbers, email addresses, transaction records, etc. This raises a critical question: how did this data fall into the hands of scammers?
Yesterday, Mike Dudas, co-founder of The Block, stated on the X platform that he received an unsettling email from Coinbase. The email pointed directly to internal data access issues. It stated:
“We are writing to inform you that we have detected signs indicating that a Coinbase employee may have accessed a small number of Coinbase customer account records in a manner inconsistent with internal policies, including your account.”
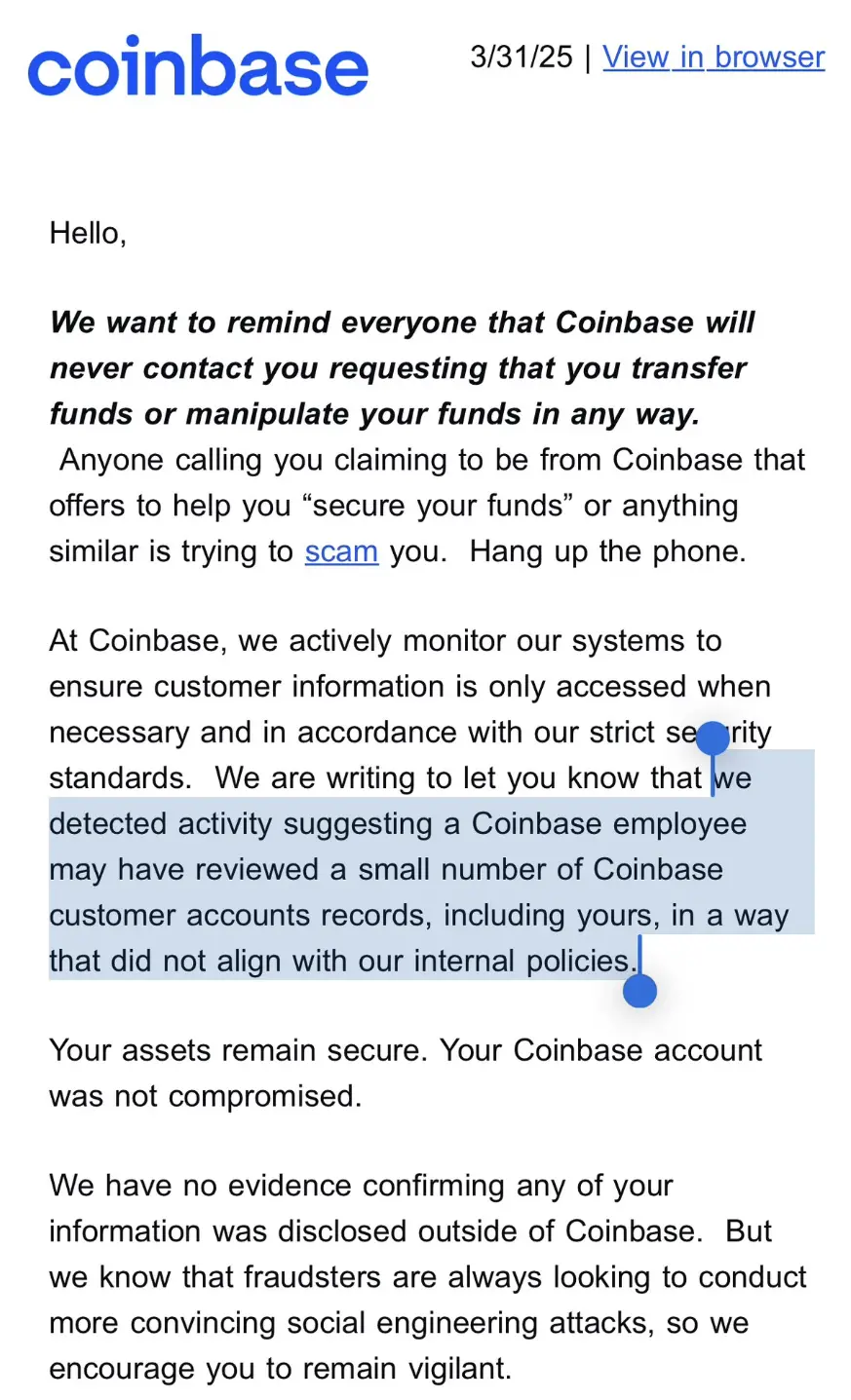
Although the email stated, “Your assets are still safe, and your Coinbase account has not been compromised,” and emphasized that there is currently no evidence that data has leaked externally, this email sent a clear warning to users: internal data access issues have been confirmed and are not isolated incidents.
Dudas noted, this explains the phishing emails and calls impersonating Coinbase that have surfaced today.
However, the scope of the data breach is questionable and may involve a broader range of users. Community user @ghaiankur stated, “I have no funds on Coinbase and have never used it. Yet I still received these emails because I have an account, which may not just target a few accounts but the entire database.”
Data Breaches Become Industry Hazards
Not only Coinbase, but other exchanges also seem to face similar internal security vulnerabilities.
After Dudas shared the email, crypto trader Jordan Fish (@Cobie) revealed that the crypto exchange Kraken has also recently encountered similar attacks. He speculated, “This could be the attackers' strategy—infiltrating the customer service team to steal user data from within.”
Meanwhile, on March 27, the dark web news site Dark Web Informer reported that a hacker codenamed AKM69 claimed to possess a large amount of private information from users of the crypto exchange Gemini. The database contains 100,000 records, including full names, emails, phone numbers, and location information of U.S. users, as well as data from some users in Singapore and the UK.
Either learn to protect users, or be abandoned by them.
Solana co-founder toly commented on this incident, stating that exchanges should implement user-controlled transfer time locks to reduce the risk of assets being quickly stolen. However, the essence of this incident goes far beyond that; it exposes the failure of internal risk control at exchanges and the highly industrialized nature of scam activities.
The security of exchanges is no longer just a matter of technical protection; it is also a matter of management and trust. In the face of increasingly complex attack methods, how to establish a more comprehensive risk control system will determine the future safety standards of the industry.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




