Written by: Eric, Foresight News
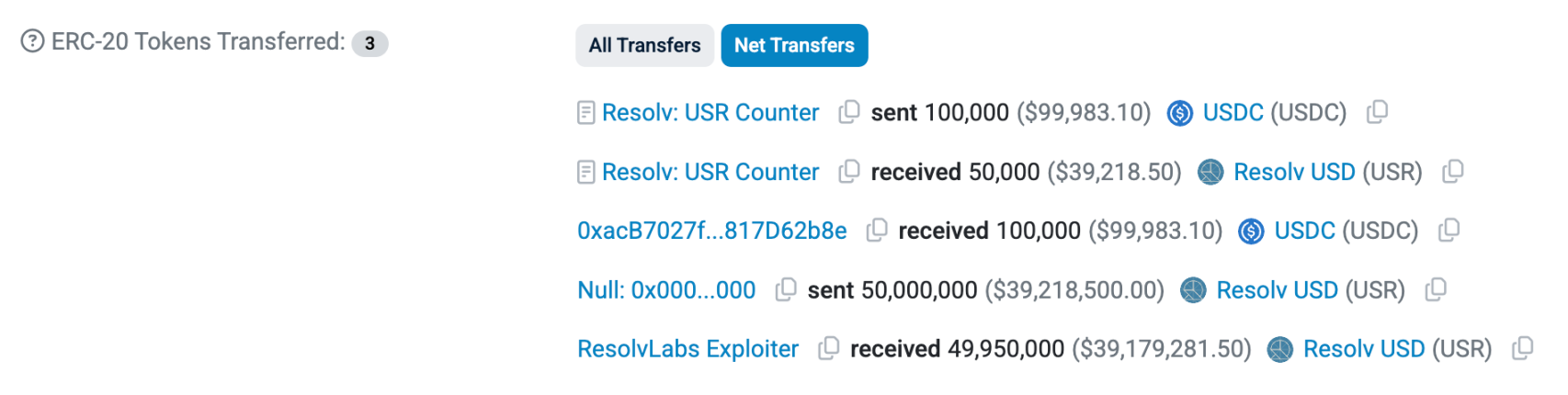
At around 10:21 Beijing time today, Resolv Labs, which issues the stablecoin USR using a Delta neutral strategy, was attacked by hackers. An address starting with 0x04A2 minted 50 million USR from the Resolv Labs protocol using 100,000 USDC.
As the incident came to light, USR dropped to around $0.25, and by the time of writing, it had recovered to about $0.8. The price of the RESOLV token also saw a temporary drop of nearly 10%.
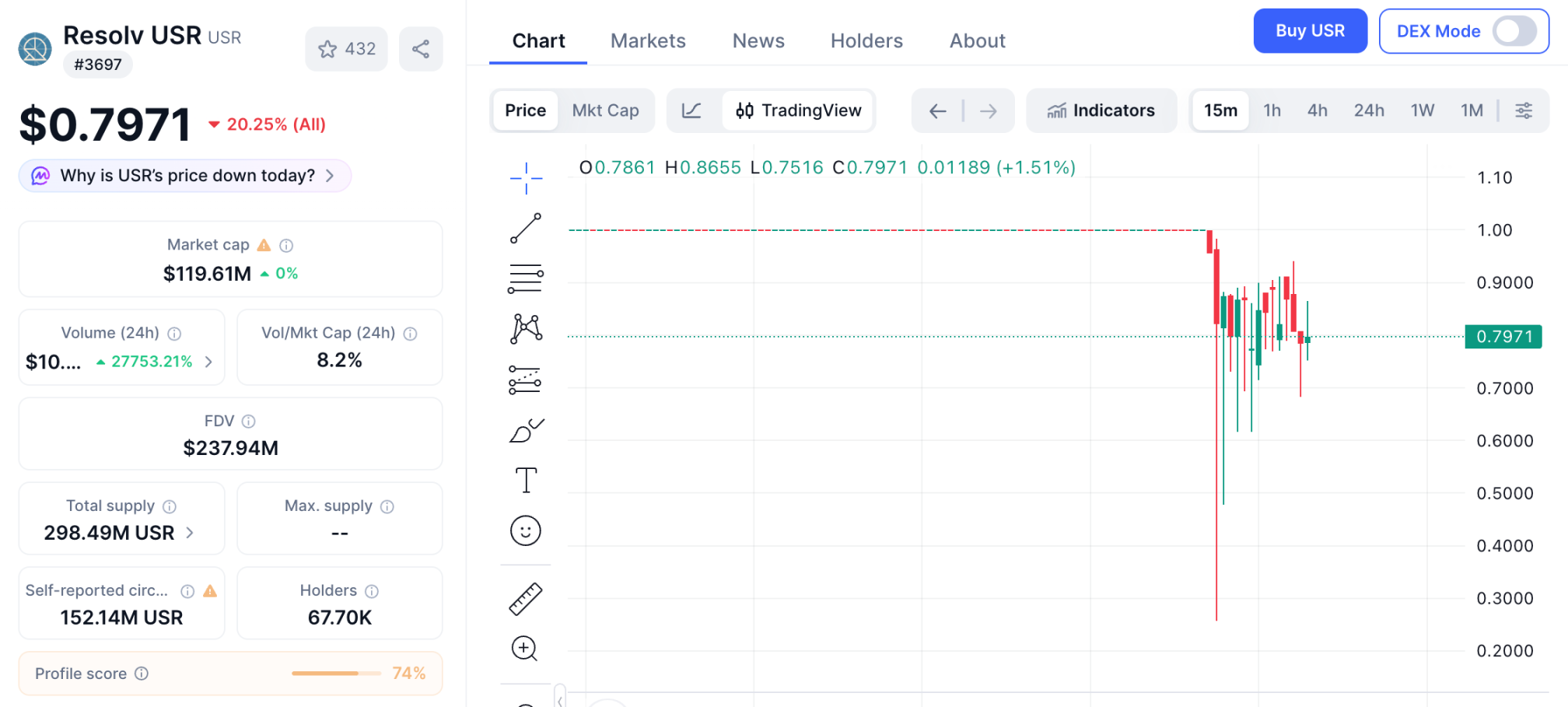
Later, the hacker repeated the method and minted 30 million USR using another 100,000 USDC. With the significant decoupling of USR, arbitrage traders quickly acted, and many lending markets supported by Morphos that accept USR, wstUSR, and others as collateral have been nearly emptied, while Lista DAO on the BNB Chain suspended new loan requests.

And it's not just these lending protocols that are affected. In Resolv Labs' protocol design, users can also mint a more volatile RLP token, which has higher yields but requires compensation when the protocol incurs losses. Currently, the circulating supply of RLP tokens is nearly 30 million, with the largest holder, Stream Finance, holding over 13 million RLP, with a net risk exposure of around $17 million.
Indeed, Stream Finance, which had previously suffered due to the xUSD incident, may be hit again.
As of the time of writing, the hacker has converted USR to USDC and USDT and has continued to purchase Ethereum, having bought over 10,000 so far. Using 200,000 USDC, they extracted assets worth over $20 million, finding their own "hundredfold coin" during the bear market.
Once again exploited due to "lack of rigor"
The crash on October 11 last year caused many stablecoins issued using the Delta neutral strategy to incur collateral losses due to ADL (automatic deleveraging). Some projects that had assets executing strategies using altcoins suffered even heavier losses or directly exited the market.
This time, the attacked Resolv Labs also issued USR using a similar mechanism. The project announced in April 2025 that it completed a $10 million seed round led by Cyber.Fund and Maven11, with participation from Coinbase Ventures, and launched the RESOLV token in late May or early June.
However, the reason for the attack on Resolv Labs was not an extreme market condition, but rather that the design of the USR minting mechanism was "not rigorous enough."
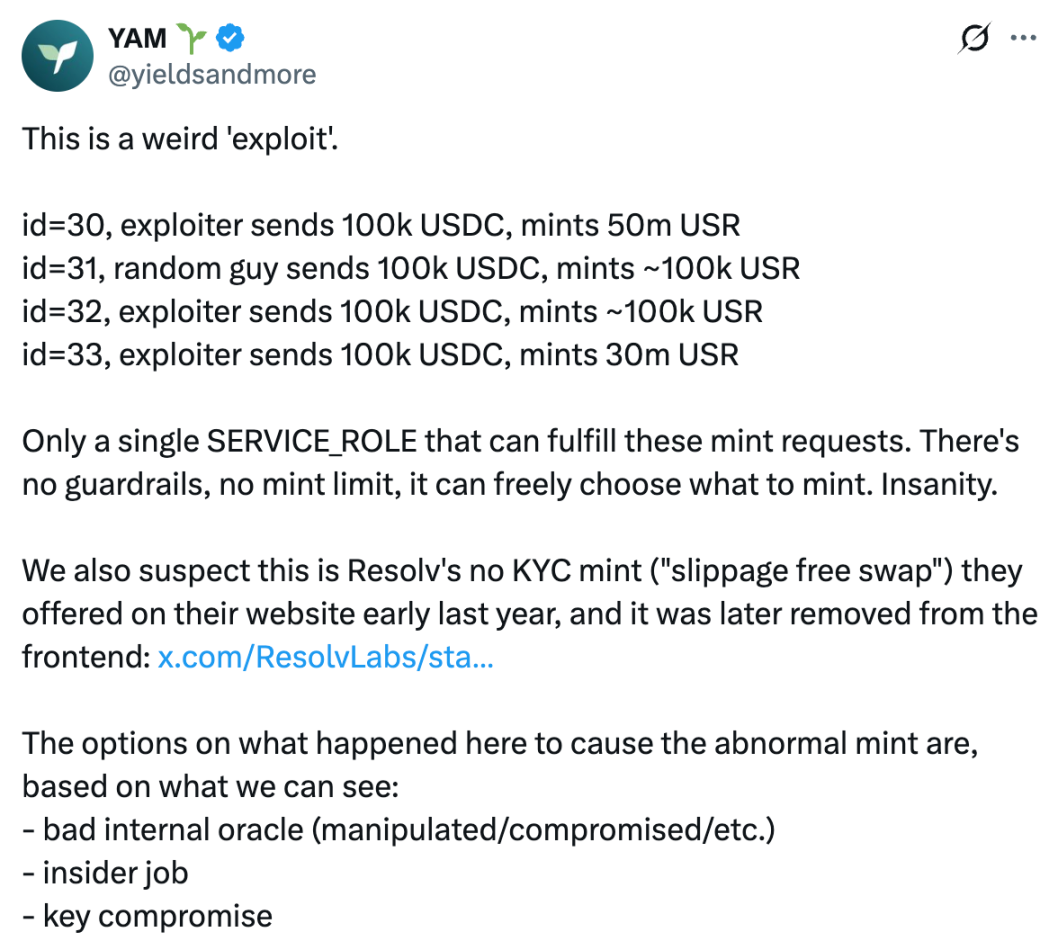
So far, no security company or official analysis has been conducted on the causes of this hacking incident. The DeFi community, YAM, preliminarily concluded through analysis that the attack was likely due to the SERVICE_ROLE used by the protocol's backend to provide parameters for the minting contract being compromised by hackers.
According to Grok's analysis, when users mint USR, they initiate a request on-chain and call the contract's requestMint function, with parameters including:
_depositTokenAddress: The address of the deposited token;
_amount: The amount deposited;
_minMintAmount: The minimum expected amount of USR (slippage protection).
Afterwards, users deposit USDC or USDT into the contract, while the backend SERVICE_ROLE monitors the requests, uses the Pyth oracle to check the value of the deposited assets, and then calls the completeMint or completeSwap function to determine the actual minted amount of USR.
The problem lies in the fact that the minting contract fully trusts the _mintAmount provided by SERVICE_ROLE, believing that this number has been verified off-chain by Pyth, thus not setting an upper limit and not verifying on-chain with an oracle, executing mint(_mintAmount) directly.
Based on this, YAM suspects the hacker controlled the SERVICE_ROLE, which should have been controlled by the project team (possibly due to internal oracle failure, insider theft, or key theft), directly setting _mintAmount to 50 million during minting, resulting in the attack event where 100,000 USDC minted 50 million USR.
Ultimately, Grok concludes that Resolv did not consider the possibility that the address (or contract) used to receive user mint requests could be controlled by hackers when designing the protocol. When the request to mint USR was submitted to the contract that ultimately mints USR, no maximum mint amount was set, nor was there a secondary verification by an on-chain oracle; they directly trusted all parameters provided by SERVICE_ROLE.
Prevention measures also inadequate
In addition to speculating on the cause of the breach, YAM also pointed out that the project team was unprepared in responding to the crisis.
YAM stated on X that Resolv Labs only paused the protocol 3 hours after the hacker's first attack, with about an hour of that delay due to collecting the 4 signatures needed for multi-signature transactions. YAM believes that an urgent pause should only require one signature, and permissions should be allocated to team members or trusted external operators as much as possible to increase awareness of on-chain anomalies and improve the possibility of a quick pause, thereby better covering different time zones.
Although the suggestion to pause the protocol with a single signature seems a bit radical, requiring multiple signatures across different time zones to pause the protocol could indeed delay critical actions during emergencies. Introducing trusted third parties for continuously monitoring on-chain behaviors or using monitoring tools with emergency pause permissions are lessons learned from this incident.
Hacker attacks on DeFi protocols are no longer limited to contract vulnerabilities; the incident at Resolv Labs serves as a warning to project teams: assumptions regarding protocol security should not trust any single link. Every aspect involving parameters must undergo at least secondary verification, even when managed by the project team itself.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



