Author: Chloe, ChainCatcher
In September 2025, the multi-signature wallet of the Web3 social platform UXLink was ruthlessly robbed, with hackers stealing over ten million dollars in assets in just a few hours and maliciously crashing the token price by minting a huge amount of tokens, resulting in an instant drop of over 70%. However, the most absurd aspect of this disaster was not the attack itself, but the hacker's “amateur” performance afterward.
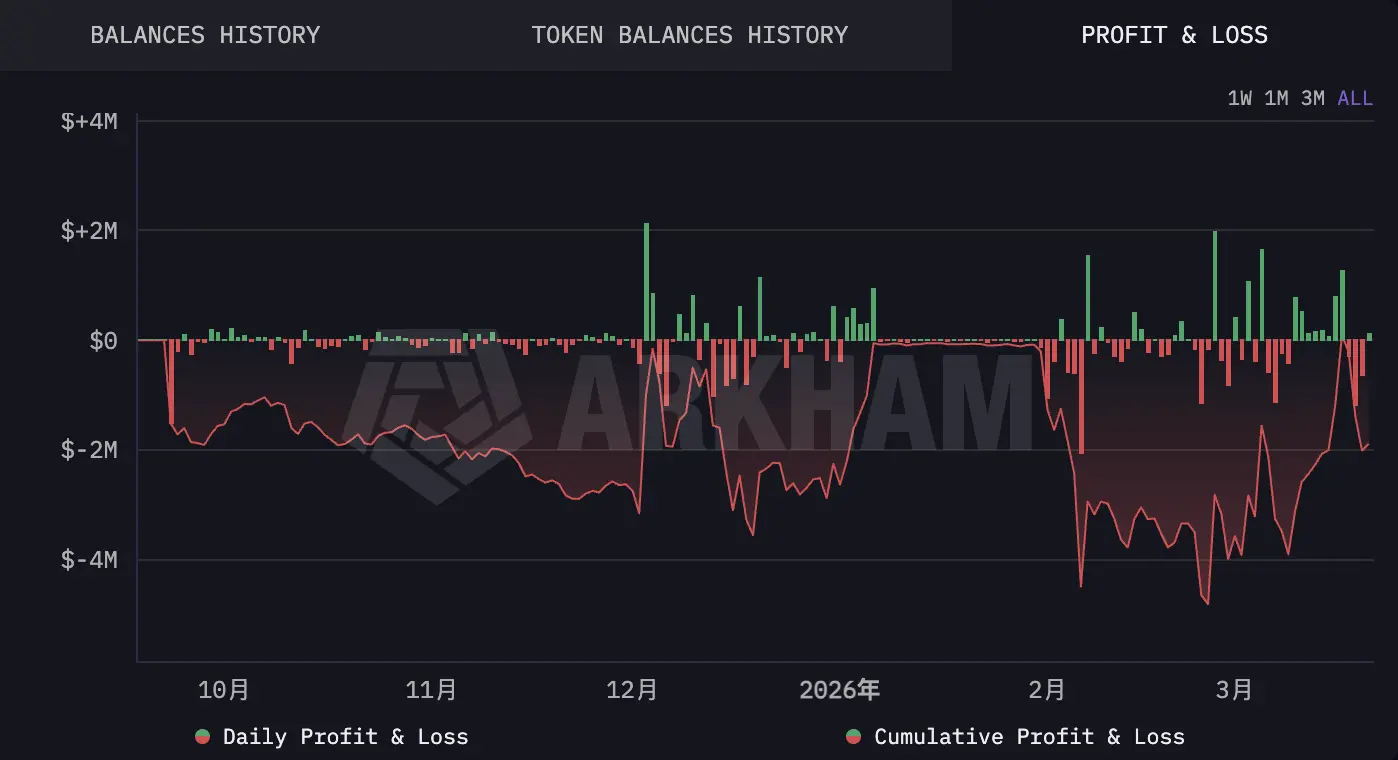
Unlike typical money laundering schemes, this hacker was not in a hurry to disappear; instead, he actively traded the stolen ETH and stablecoins on DEX, frequently trading on CoW Swap. According to Arkham's on-chain data, this address accumulated nearly 625 transactions within just six months, with paper losses reaching as high as 4.8 million dollars at one point.
Analyzing the technical path of this attack reveals the hacker's unusual behavior pattern and the harsh reality behind it: In this bear market cycle, even with advanced technology to steal money on the chain, once back in market trading, everyone is treated equally.
UXLink Multi-Signature Wallet Security Vulnerability, Loss Exceeding Ten Million Dollars
Blockchain security company Cyvers was the first to detect unusual activity in the UXLink multi-signature wallet on September 22, 2025, and issued an emergency alert. Subsequently, UXLink officials confirmed that their core multi-signature wallet had been breached, resulting in losses exceeding 11.3 million dollars.
The technical path of this attack is quite clear; the hacker targeted the delegateCall function vulnerability in the multi-signature wallet, successfully altering the contract logic. The attacker first removed the legitimate administrative rights of the wallet; then while calling the addOwnerWithThreshold function, forcibly implanted himself as a new wallet owner. Thus, the multi-signature security mechanism vital to UXLink was completely bypassed, and the control of the wallet was entirely transferred.
What followed was a rampant plundering of on-chain assets. The list of stolen assets included approximately 4 million dollars in USDT, 500,000 dollars in USDC, 3.7 WBTC, 25 ETH, and native tokens UXLINK worth about 3 million dollars. Meanwhile, the hacker minted a massive amount of UXLINK tokens on the Arbitrum chain and flooded the market, causing the token price to plummet over 70% in a short time, dropping from about 0.30 dollars to below 0.10 dollars, with a market cap evaporating over 70 million dollars.

Taking Unconventional Routes: Abandoning Money Laundering and Staying in On-Chain Trading
According to the typical script for cryptocurrency crimes, the next plot should unfold like this: the hacker would funnel the assets into Tornado Cash for anonymization, washing them out through countless jump addresses, ultimately completing the entire money laundering and cash-out process. However, this attacker chose not to follow the conventional route.
About 48 hours after the attack, the hacker exchanged 1,620 ETH for approximately 6.73 million DAI, which should have been the first wave of "cash-out" signals expected by the market. Several on-chain analysts quickly identified this on-chain behavior, but in the following six months, this address's behavior completely deviated from the calm and secrecy typical of professional hackers, instead starting to engage in frenzied trading on-chain.
According to Arkham's on-chain data tracking, this address accumulated as many as 625 transaction records within just six months, with activities highly concentrated on the decentralized trading platform CoW Swap. Its trades frequently moved back and forth between WETH and DAI, with a trading frequency far exceeding typical long-term holders. Thus, rather than being a hacker who stole millions of dollars, he resembled more of a trader or a retail investor accustomed to "buying the dip, holding through volatility, and exiting near the cost line."
Poor Trading Skills: Paper Losses Exceeding 4 Million Dollars, Nearly Stagnating for Six Months
According to Arkham's profit and loss tracking data, from October 2025 to early February 2026, the attacker’s address often showed paper losses exceeding 3 million dollars; entering February, the losses even reached a peak of 4.8 million dollars. Its trading pattern was highly consistent: continuously increasing positions at lows and stubbornly holding through volatility, until prices finally rose close to the cost line before choosing to exit.
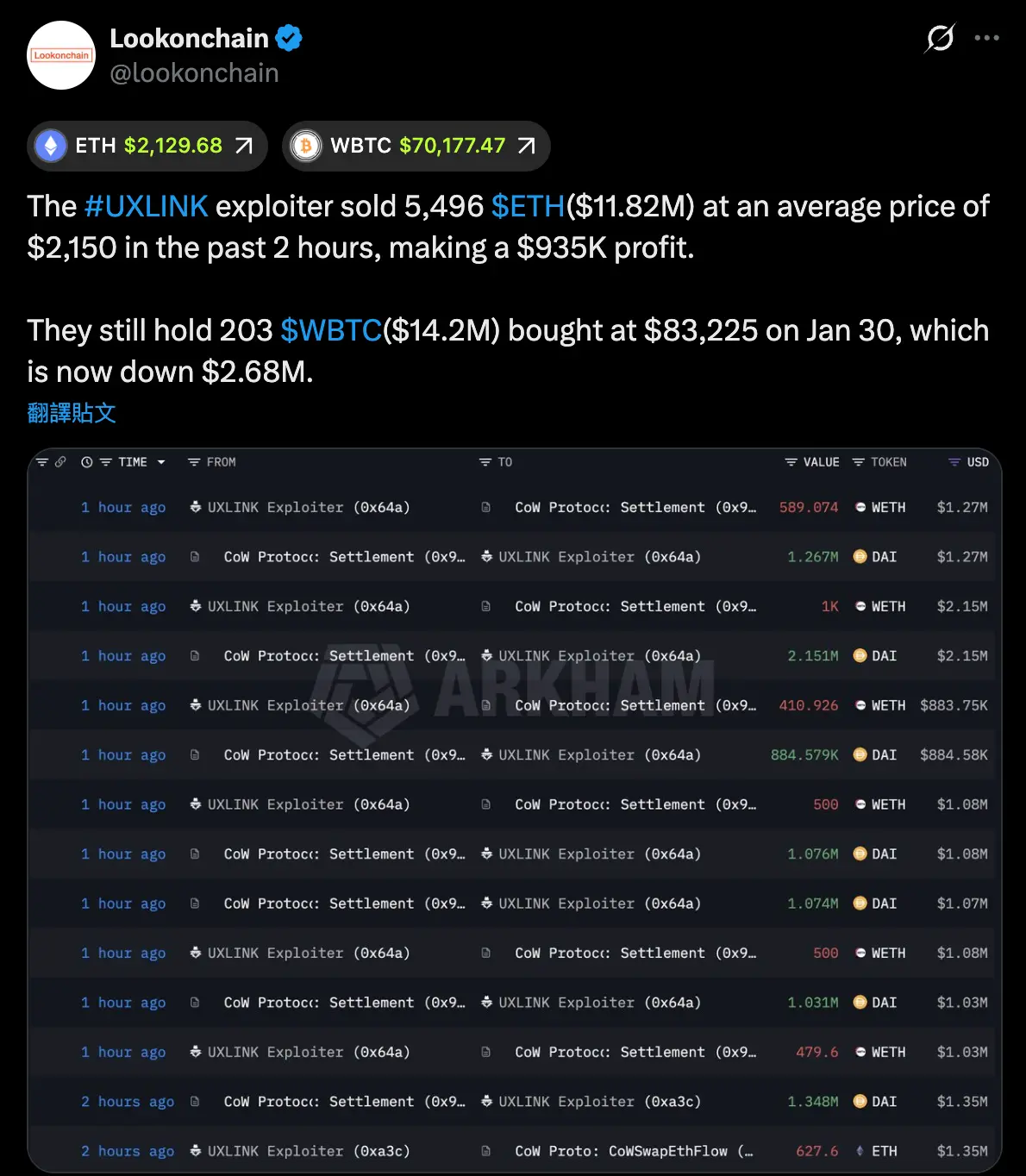
By late March, the hacker finally saw a turnaround. On CoW Swap, he exchanged 5,496 ETH for about 11.86 million DAI at an average price of 2,150 dollars. This operation brought him a paper profit of about 935,000 dollars, and his overall investment portfolio finally returned to the breakeven line. However, the concurrently held WBTC positions were eroding this profit; on January 30, 2026, the hacker bought 203 WBTC at an average price of 83,225 dollars, and as of recently, he had paper losses of approximately 2.68 million dollars, as this entry perfectly coincided with a short-lived market rebound, and once again, he bought at relatively high levels.
Transparent Prison and Long Path to Recovery
The UXLink incident provides a unique perspective on the history of cryptocurrency crimes: an attacker under the spotlight, continuously leaving highly visible transaction tracks, allowing global on-chain analysts to fully document his behavioral process.
This may not stem from the hacker's negligence but from an outdated understanding of "security." He might believe that as long as assets are spread across multiple addresses and operations are carried out on DEX to avoid the real-name verification barriers of CEX, he can maintain anonymity. However, the evolution of on-chain analysis tools has made such judgment overly optimistic. Institutions like Arkham, Lookonchain, PeckShield, and Slow Mist nearly instantaneously lock in each major abnormal movement; every entry and exit of the hacker is laid bare under public scrutiny. Though this hacker possessed millions of dollars, it was as if he was in a transparent digital prison.
For the UXLink project team, this situation is both somewhat comforting and a significant dilemma. Although the assets have not disappeared and remain on a traceable blockchain, in a world where there is no judicial jurisdiction to intervene, the gulf between “visibility” and “retrievability” still looms large.
Although UXLink quickly completed new contract auditing, token exchange, and user compensation programs after the incident, attempting to rebuild market confidence, the token price has fallen from its peak of 3.75 dollars in December 2024 to about 0.0044 dollars, a drop of 99%. For UXLink, patching the code vulnerabilities may only take a few weeks, but rebuilding the ecosystem from the near-zero ruins still remains a long and arduous road.
Facing the Bear Market, Everyone is Treated Equally
The story of the UXLink hacker has become a microcosm of "market reality," rather than merely a security incident.
While he possesses excellent skills, able to precisely capture vulnerabilities in delegateCall and bypass multi-signature defenses, completing a meticulously planned harvest within mere hours; however, after the funds entered his account, he faced the same predicament as any ordinary retail investor: the market does not care where the chips came from, ETH continued to drop during his holding period, and BTC was still stuck after his entry.
This outcome holds no need for compassion, yet it is filled with irony. The assets the attacker painstakingly stole ultimately wore down amidst market volatility, and after six months, their paper value was almost the same as at entry. He is not the first ETH holder to suffer losses in a bear market, nor will he be the last speculator to be bitten by the market when trying to bottom fish for WBTC.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




